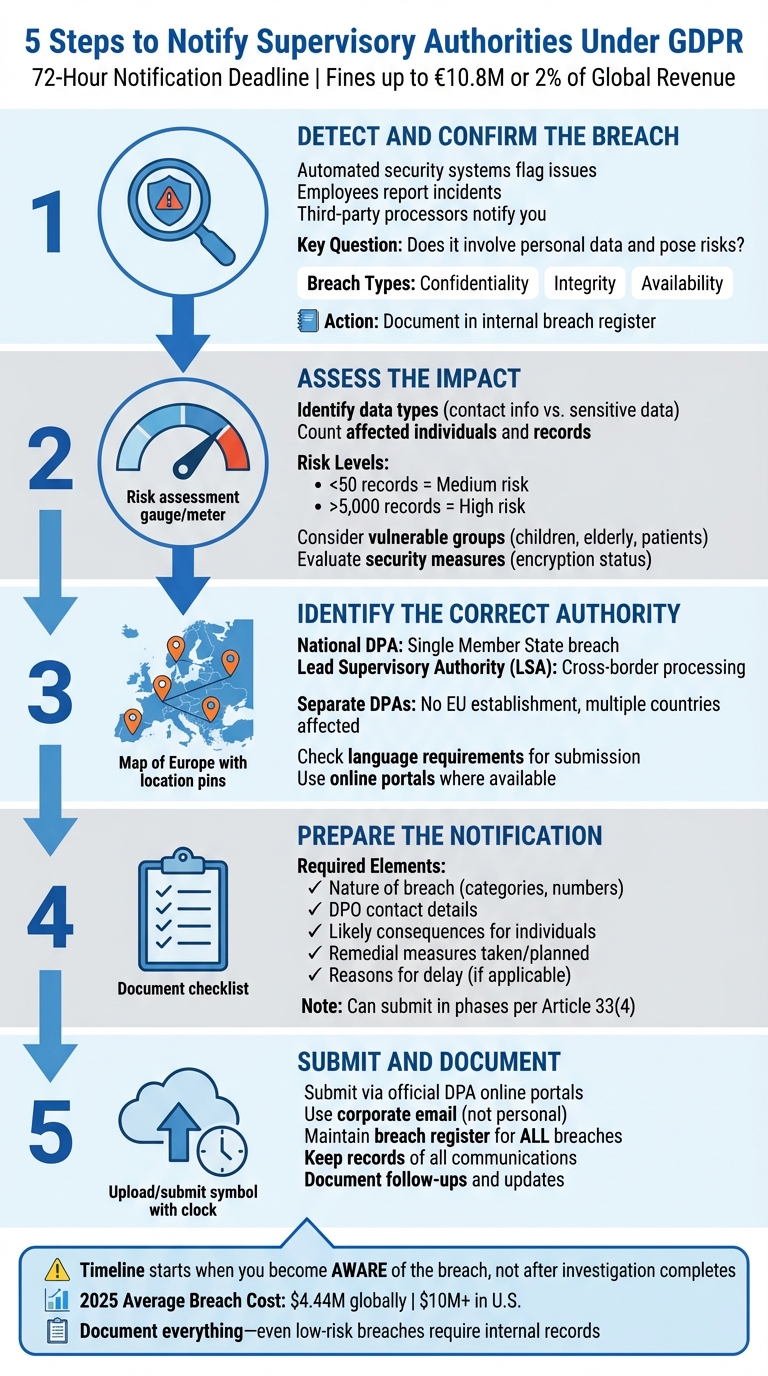
5 Steps to Notify Supervisory Authorities Under GDPR

When a personal data breach occurs, GDPR requires you to notify the appropriate supervisory authority within 72 hours. This timeline starts when your organization becomes aware of the breach, not after completing your investigation. Missing this deadline or failing to document the breach properly can lead to fines reaching $10.8 million or 2% of your global revenue. Here's a quick summary of the five steps you need to follow:
- Detect and Confirm the Breach: Identify if the incident involves personal data and assess whether it poses risks to individuals' rights.
- Assess the Impact: Evaluate the severity of the breach based on the type of data, number of individuals affected, and potential harm.
- Identify the Correct Authority: Determine whether to notify a national Data Protection Authority (DPA) or a Lead Supervisory Authority (LSA) for cross-border cases.
- Prepare the Notification: Include key details like the nature of the breach, affected data, potential consequences, and remedial measures.
- Submit and Document: File the notification within 72 hours, even if incomplete, and maintain thorough records for audits.
Key takeaway: Timely action and detailed documentation are critical to staying compliant and minimizing risks.
5 Steps to Notify Supervisory Authorities Under GDPR Within 72 Hours
GDPR Data Breach Notification - The 72 hours notification
sbb-itb-5f36581
Step 1: Detect and Confirm the Data Breach
A data breach can come to light in several ways. Automated security systems might flag issues like ransomware attacks or unauthorized access attempts. Employees could report incidents such as misdirected emails or lost devices. Sometimes, third-party data processors might notify you of a breach. According to Article 33(8) of the GDPR, processors are required to inform controllers "without undue delay" once they discover a breach.
After identifying a potential breach, the next step is to confirm whether it meets the GDPR's criteria for a personal data breach. Breaches typically fall into one of these three categories:
- Confidentiality: Unauthorized access or disclosure, such as a stolen unencrypted laptop.
- Integrity: Unauthorized alteration, like ransomware encrypting files.
- Availability: Loss of access or destruction, such as permanent data loss without a backup.
"Awareness means having certainty that a security incident has compromised personal data." – C B Sekhar, Founder & CEO, Glocert International
To determine if an incident qualifies as a breach, ask: Does it involve personal data of identifiable individuals, and does it pose a risk to their rights? If the data was encrypted with strong methods and the encryption keys remain secure, it might not count as a reportable breach. Regardless, every incident must be documented in an internal breach register. Regulators can review these records during audits, even if the breach doesn't require notification.
When documenting the breach, follow an escalation workflow: Detect, Report, Escalate to the DPO, Secure the data, and Assess the scope and risk. In the first four hours, prioritize stopping any ongoing access and preserving evidence, such as logs and screenshots. Identify the types of personal data involved, estimate the number of individuals and records affected, and consider whether vulnerable groups, like children, are impacted. This process lays the groundwork for evaluating the breach's impact and associated risks.
Step 2: Assess the Impact and Scope of the Breach
After confirming a breach, the next step is to evaluate its severity by identifying the types of compromised data. For example, basic contact information carries less risk compared to sensitive data like financial records, health information, or account credentials. It's also important to determine the number of individuals and records affected. Breaches involving fewer than 50 records are generally considered medium risk, while those exceeding 5,000 records often fall into the high-risk category.
You’ll also need to consider how the breach might affect individuals. Recital 85 of the UK GDPR highlights that breaches can lead to both tangible and intangible harm, such as identity theft, fraud, or economic and social disadvantages. This is especially critical when vulnerable groups - like children, the elderly, or patients - are involved, as their inclusion automatically raises the risk level.
To assess the overall risk, combine the potential impact with the likelihood of harm. A common approach is using a scoring system, where factors like data sensitivity, volume, identifiability, harm potential, and containment are rated on a 1–5 scale. Breaches scoring above 15 are generally flagged as high risk.
Additionally, evaluate whether existing security measures, such as encryption, help reduce the breach's risk. Strong encryption with secure keys and prompt containment can significantly lower the risk level. These measures often distinguish low-risk breaches from high-risk ones.
Low-Risk vs. High-Risk Breaches
Understanding what separates low-risk breaches from high-risk ones is crucial for deciding your next steps. Low-risk breaches typically involve encrypted or pseudonymized data, affect a small number of general adult users, and are contained quickly before causing harm. These breaches usually require internal documentation but don’t always necessitate notifying a supervisory authority.
High-risk breaches, on the other hand, involve unencrypted sensitive data - like health records, financial information, or account credentials - that could lead to identity theft, fraud, or even physical harm. The risk escalates further if vulnerable individuals are impacted or if the data is made publicly accessible. In such cases, you must notify the supervisory authority within 72 hours and inform the affected individuals, as required under Article 34.
| Factor | Low-Risk Characteristics | High-Risk Characteristics |
|---|---|---|
| Data Type | Contact info, publicly available data | Health, biometric, financial info, passwords |
| Security State | Strong encryption (key not compromised) | Unencrypted plain text, compromised credentials |
| Affected Population | General adult population | Children, vulnerable adults, patients |
| Containment | Immediate recovery before access | Data publicly accessible, unauthorized external access |
| Individual Impact | Minimal inconvenience | Identity theft, fraud, discrimination, loss of account control |
Even low-risk breaches require thorough documentation of the incident, its effects, and the actions taken. Regulators may request these records during audits, and failing to maintain proper documentation can result in fines of up to $10.8 million or 2% of global annual turnover.
Step 3: Identify the Correct Supervisory Authority
Once you've assessed the breach's impact, the next step is pinpointing the right supervisory authority to notify. This depends on your organization's main establishment and the breach's scope. Your main establishment is essentially where your central administration is located and where key decisions about data processing are made.
For breaches that cross borders and affect multiple Member States, you’ll need to notify the designated Lead Supervisory Authority (LSA). This is part of the "one-stop-shop" mechanism that simplifies compliance. As outlined in Article 56 of GDPR: "The lead supervisory authority shall be the sole interlocutor of the controller or processor for the cross-border processing carried out by that controller or processor". Getting this right is crucial to meet the 72-hour notification deadline and to stay compliant.
If your organization is based outside the EEA, you’ll need to notify each Data Protection Authority (DPA) in the countries where affected individuals reside. For example, a U.S.-based company with no EU office that experiences a breach impacting users in Germany, France, and Spain must submit separate notifications to all three national authorities.
Before filing, check the language requirements for each DPA. While some, like those in Denmark, Estonia, and Finland, accept English, others require submissions in their native language (e.g., French for France's CNIL or Italian for Italy's Garante). Many DPAs, such as Ireland's Data Protection Commission and Germany's BfDI, offer online portals with dedicated breach notification forms.
National vs. Lead Supervisory Authority
Understanding the difference between a national supervisory authority and a Lead Supervisory Authority helps clarify your notification process. A national authority deals with breaches affecting individuals in a single Member State, while a Lead Supervisory Authority oversees cross-border cases.
If your breach is contained within one country where you have an establishment, the local DPA will likely be your key contact. However, they are required to inform the LSA within three weeks. For cross-border incidents, the LSA becomes your primary point of contact. If you're unsure which authority to notify and the 72-hour deadline is looming, notify at least the local DPA where the breach occurred to ensure compliance. For more guidance, the European Data Protection Board's Guidelines 8/2022 provide detailed criteria for determining your LSA.
Here’s a quick comparison to help you decide:
| Authority Type | When It Applies | Your Notification Approach |
|---|---|---|
| National DPA | Breach affects only one Member State; local processing only | Notify the DPA in that specific country |
| Lead Supervisory Authority | Cross-border processing; main establishment in EU/EEA | Notify your LSA using the one-stop-shop mechanism |
| Separate DPAs | No EU/EEA establishment; affects multiple countries | Notify every DPA where affected individuals reside |
Step 4: Prepare the Notification Content
Once you've identified the right authority to notify, it's time to put together your notification. Article 33 of the GDPR lays out exactly what needs to be included. Your notification must cover several critical points: a detailed description of the breach (including the types and approximate numbers of affected data subjects and records), contact details for your Data Protection Officer (DPO) or another designated contact, an explanation of the likely consequences for individuals, and a summary of the measures you've taken or plan to take to address the breach and reduce its impact.
When describing the breach, be specific. If 1,200 customer records were exposed, say "1,200" instead of using vague approximations like "around 1,000." Clearly state whether the breach involved unauthorized access (affecting confidentiality), unauthorized changes (affecting integrity), or data loss (affecting availability). If sensitive data is involved - such as health records, genetic information, or data about children - this increases the risk and should be explicitly noted.
The section on consequences should focus on realistic harms that individuals might face. This could include identity theft, financial fraud, reputational damage, or breaches of sensitive information. For example, if encrypted data was exposed but the encryption keys were not, explain why this lowers the risk. On the other hand, if login credentials were compromised, acknowledge the potential for account takeovers.
For remedial actions, separate what you've already done from what you plan to do. Immediate steps might include isolating systems, resetting passwords, or securing affected servers. Planned actions could involve rolling out security updates, conducting staff training, or improving monitoring systems. By outlining these steps, you show the supervisory authority that you're actively working to manage the situation.
Required Elements for a Complete Notification
| Required Element | What to Include |
|---|---|
| Nature of Breach | Categories and approximate number of affected data subjects and records |
| Contact Details | Name and contact information for the DPO or relevant contact point |
| Likely Consequences | Potential physical, material, or emotional harm to individuals |
| Remedial Measures | Steps taken or planned to address the breach and mitigate risks |
| Reasons for Delay | Necessary only if the notification is submitted after the 72-hour deadline |
Providing the DPO’s contact details is critical and should be done immediately, even if other parts of the notification are still being finalized. This ensures the supervisory authority can reach out with follow-up questions as needed.
Managing Delays or Incomplete Notifications
The 72-hour clock starts ticking once you have a reasonable level of certainty that a breach has occurred - not necessarily when the breach itself happened. If you're waiting on forensic evidence or further analysis from your IT team, don’t delay the notification until you have all the details. Article 33(4) allows for phased reporting, so you can submit an initial report with the information you have and follow up later as more details become available.
"Where, and in so far as, it is not possible to provide the information at the same time, the information may be provided in phases without undue further delay." - GDPR Article 33(4)
If you miss the 72-hour deadline, your notification must include a formal explanation for the delay. Acceptable reasons might include waiting on essential information from a third-party processor or needing additional time to understand the full scope of a complex breach. However, excuses like "we were too busy" or "we didn’t realize the deadline" won’t fly. Failing to notify on time is a separate GDPR violation, which can lead to fines of up to $10.8 million or 2% of your organization’s total global annual revenue from the previous year, whichever is higher.
Once your notification is complete and any potential delays are addressed, you’re ready to submit your report and move on to maintaining thorough records in the next step.
Step 5: Submit the Notification and Maintain Documentation
Submitting Notifications via Online Portals
Once your notification content is ready, the next step is to submit it through the appropriate channels and ensure everything is properly documented. Most Data Protection Authorities (DPAs) in the EEA provide online portals to make submitting notifications more efficient. For instance, Spain's AEPD requires the use of its official online form and does not accept email submissions. Before starting, confirm the portal's authentication method (e.g., Estonia uses eID or Mobile-ID) and language requirements - Austria requires submissions in German, while Norway accepts Norwegian, Danish, Swedish, or English.
When submitting, it's crucial to use your organization's corporate email address, as notifications sent from personal accounts might be rejected. If you're nearing the 72-hour deadline and don't have all the details, you can submit preliminary information. Many of these portals allow phased reporting, enabling you to provide updates as more information becomes available.
Documenting Compliance
After submitting the notification, thorough documentation is key to demonstrating compliance. Under Article 33, controllers are required to maintain a breach register that logs every personal data breach, even those considered low risk. This ensures a clear record of breach management practices and supports your decision-making during audits.
Your documentation should include all the details shared with the DPA: the nature of the breach, the categories and number of affected individuals and records, contact information for your Data Protection Officer (DPO), potential consequences, and the steps taken to address the issue. If you submitted information in phases, keep records of follow-up communications and any reasons for initial omissions. For breaches involving high risks where affected individuals were notified, retain copies of those notifications as well.
For example, in June 2025, SimonMed Imaging, a major U.S. medical imaging provider, experienced a breach impacting approximately 1.27 million individuals. The breach exposed names, medical records, and insurance details. The company documented its response, which included resetting credentials, implementing multi-factor authentication, and enhancing endpoint monitoring. Similarly, in October 2025, Discord reported a breach involving its customer support vendor, 5CA, which exposed data from 70,000 users. Discord responded by revoking the vendor's access, hiring a digital forensics firm, and notifying law enforcement and data protection authorities. These examples highlight the importance of detailed documentation in maintaining accountability and ensuring compliance.
Conclusion
Under GDPR, notifying supervisory authorities is mandatory as soon as your organization becomes aware of a breach. The 72-hour countdown begins when there’s a reasonable certainty that an incident has occurred - not when the investigation is fully completed. Failing to meet this deadline or providing inadequate documentation can result in separate violations, each carrying hefty penalties. Additionally, every breach must be recorded in an internal register to meet audit requirements.
To handle breaches effectively, follow these five key steps: detect and confirm the breach, assess its impact, identify the appropriate supervisory authority, prepare the notification, and submit it with all required documentation. This structured approach safeguards your organization and the affected individuals.
The stakes are high - both financially and reputationally. In 2025, the global average cost of a data breach was $4.44 million, but U.S. organizations faced costs exceeding $10 million, largely due to stricter regulatory penalties. Beyond financial losses, mishandling a breach can damage your reputation. As Konfirmity highlights, a poorly executed breach response can drive away potential customers, even if other compliance measures are in place.
FAQs
What counts as “awareness” that starts the 72-hour clock?
Under GDPR, the 72-hour clock begins ticking the moment an organization has a reasonable level of certainty that a security incident has occurred and personal data has been compromised. While complete details aren't necessary at this stage, there must be sufficient evidence to confirm that the breach involves personal data.
Do I still need to notify if the breached data was encrypted?
If the compromised data was encrypted in a way that renders it unreadable to unauthorized individuals, you might not be obligated to notify the supervisory authority under GDPR. However, if the breach still poses a risk to individuals' rights and freedoms, notification becomes mandatory. When encryption successfully reduces this risk, reporting the breach may not be required.
Which supervisory authority should I notify for cross-border breaches?
When dealing with cross-border breaches, it's important to notify the supervisory authority located in the country where your company’s main establishment or primary decision-making hub is based. If your business operates across several EU Member States, you'll need to determine your lead supervisory authority by identifying your main establishment. Keep in mind, data subjects have the right to file complaints with any EU/EEA authority. If necessary, these authorities can transfer the case to the appropriate jurisdiction.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)








