Top 5 Technical Safeguards for Global Data Transfers

Key Safeguards:
- Encryption: Secure data in transit and at rest using strong encryption protocols (e.g., AES-256, TLS 1.3). Keep encryption keys within trusted jurisdictions.
- Access Controls & MFA: Limit data access with role-based permissions and enforce multi-factor authentication for added security.
- Geo-Fencing: Restrict data access and transfers based on geography to comply with local data laws.
- Logging & Monitoring: Use SIEM tools to track data movements and detect security breaches in real time.
- Data Minimization: Transfer only necessary data and apply techniques like pseudonymization to reduce risks.
Why It Matters:
- Non-compliance can lead to criminal penalties, fines, or even prison sentences.
- Safeguards help mitigate risks like government surveillance or unauthorized access during cross-border transfers.
These measures aren’t just about compliance - they’re about protecting sensitive data in a complex regulatory landscape. Start implementing them today to avoid costly consequences.
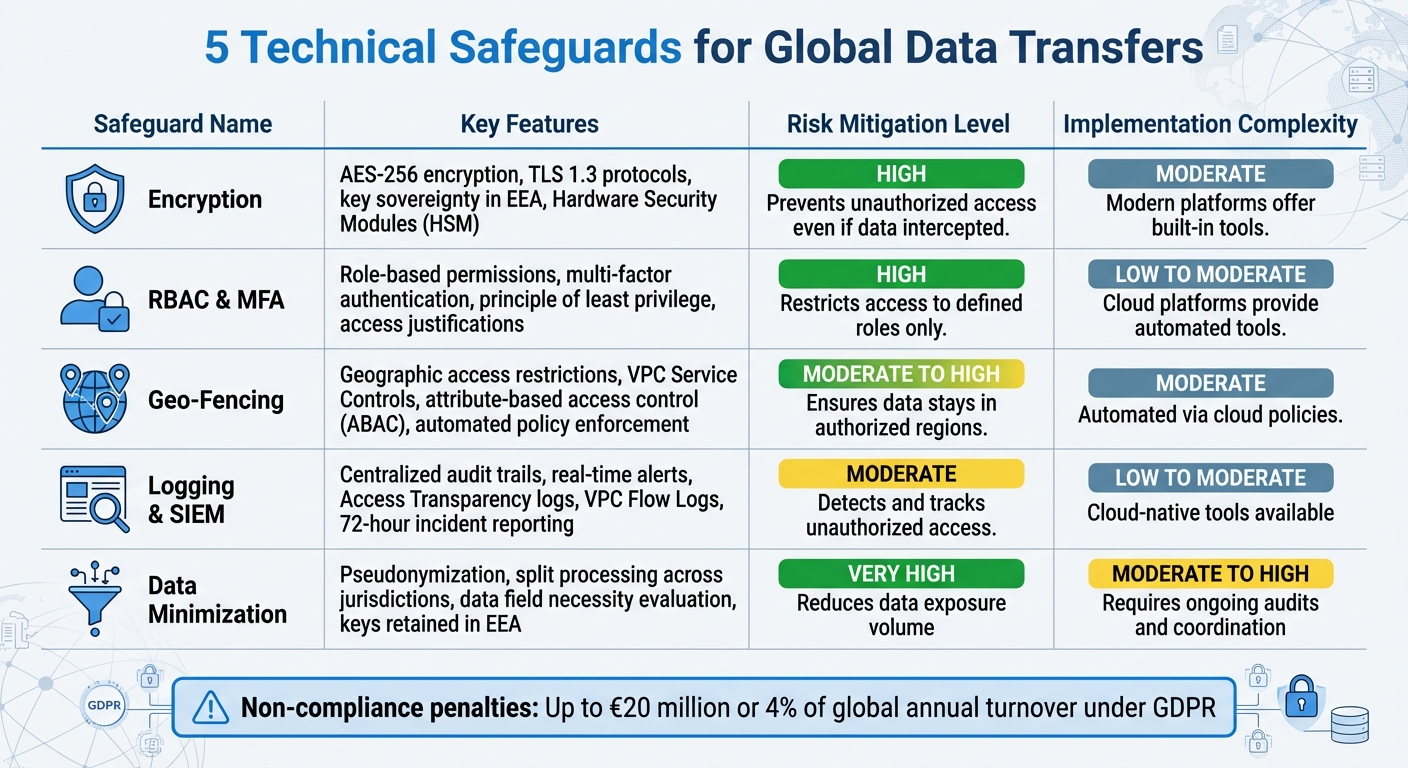
5 Technical Safeguards for Global Data Transfers: Security Features and Implementation
Achieving Cross Border Data Privacy Compliance in the Enterprise With a Secure Data Service
sbb-itb-5f36581
1. Encryption for Data in Transit and at Rest
Encryption stands as a key technical safeguard for protecting data during global transfers, ensuring compliance and fortifying defenses against unauthorized access. By converting information into an unreadable format through cryptographic algorithms, encryption renders data useless to anyone without the proper decryption key. This safeguard has become crucial, particularly after the Schrems II ruling, which highlighted vulnerabilities in how some countries protect European data from government surveillance.
Data Protection and Security
Encryption works by transforming data into an unreadable format, making it indecipherable to unauthorized parties - even if intercepted by foreign government authorities or other entities. Double encryption adds an extra layer of protection by using separate keys, ensuring data remains secure even if one key is compromised.
For data in transit, protocols like TLS 1.2 and TLS 1.3 are essential to secure information as it moves across networks. The Information Commissioner's Office (ICO) strongly advises against using outdated protocols:
"When choosing an appropriate protocol for encrypted transfer, you must not use any versions of SSL. All versions of SSL suffer from a number of well-known vulnerabilities... if you do use it, you are not complying with your obligations."
For data at rest - stored in databases, backups, or cloud environments - AES encryption standards (AES-128, AES-192, or AES-256) are widely recommended. To maximize security, encryption keys should be stored separately from the encrypted data, ideally within a secure Hardware Security Module (HSM). This ensures that even if storage systems are breached, the data remains protected.
Compliance with Global Regulations
Under GDPR Chapter V, encryption is highlighted as a key supplementary measure for transferring data to countries without an adequacy decision. The European Data Protection Board (EDPB) emphasizes the role of advanced encryption in addressing gaps in data protection when destination countries have surveillance laws that could undermine safeguards.
However, encryption is only effective if key sovereignty is maintained. According to the EDPB:
"Encryption will only suffice as an effective supplementary measure... where the cryptographic keys are retained solely under the control of the data exporter, or other entities entrusted with this task within the EEA or a third country which has been the subject of an adequacy decision."
This means that when using Standard Contractual Clauses (SCCs) to transfer data to a processor in a non-adequate country, encryption keys must remain under the data exporter's control. Ideally, they should be stored within the EEA or in jurisdictions with adequacy decisions, such as Japan, Canada (for commercial entities), or the UK as of early 2026. These requirements demonstrate how encryption not only meets legal standards but also mitigates risks tied to cross-border data transfers.
Effectiveness in Reducing Cross-Border Risks
Encryption directly addresses risks identified in Schrems II by ensuring that even if compelled disclosures occur, the data remains inaccessible due to encryption.
Before implementing encryption, conducting a Transfer Impact Assessment (TIA) is recommended. This assessment evaluates the surveillance laws of the destination country and ensures that encryption can provide adequate protection. As the EDPB notes:
"Data exporters are responsible for verifying, on a case-by-case basis, whether the law or practice of the non-EEA country impinges... on the effectiveness of the appropriate safeguards."
Ease of Implementation and Scalability
Modern platforms now offer built-in encryption tools that meet industry standards and are easy to deploy.
To scale encryption across global operations, organizations should take several steps: disable backward compatibility for protocols below TLS 1.2 to avoid downgrade attacks, implement HTTP Strict Transport Security (HSTS) to enforce encrypted connections, and automate certificate management to prevent lapses caused by expired certificates. Additionally, adopting Customer-Managed Keys (CMK) provides tighter control, allowing immediate key revocation in case of compromise.
2. Role-Based Access Controls and Multi-Factor Authentication
RBAC (Role-Based Access Control) and MFA (Multi-Factor Authentication) play a critical role in securing cross-border data transfers by tightly regulating who can access data and verifying user identities. RBAC enforces the "principle of least privilege", allowing data importers or sub-processors to access only the data they need for their specific tasks. This is especially crucial considering that roughly 90% of a company's data is unstructured, making granular access controls indispensable for safeguarding files during international transfers. Below, we explore how these elements strengthen security, compliance, and operational efficiency.
Data Protection and Security
RBAC works by limiting data access based on specific roles and data subsets, effectively minimizing the risk of unauthorized lateral movement within a system. When paired with MFA, it provides an additional layer of defense, even if primary credentials are compromised. As Google Cloud advises:
"Configure multifactor authentication (MFA) for all users who require access to sensitive data."
Furthermore, integrating Identity and Access Management (IAM) with VPC Service Controls creates a security perimeter that prevents data exfiltration - even when valid credentials are used. This approach is particularly valuable for achieving operational sovereignty, as it allows organizations to impose access restrictions based on factors like a user's nationality or location, regardless of where the data is physically stored.
Compliance with Global Regulations
In addition to enhancing security, RBAC and MFA help organizations meet the stringent requirements of global data protection regulations. Access governance is a key organizational measure recognized under GDPR to supplement Standard Contractual Clauses (SCCs), ensuring equivalent data protection in third countries. Following the Schrems II decision, these measures have become essential for compliance. For example, granting a developer in a non-adequate country access to a database - even for troubleshooting - qualifies as a cross-border data transfer, necessitating both SCCs and technical safeguards.
When conducting a Transfer Impact Assessment (TIA), organizations should document how RBAC and MFA reduce the risk of local authorities accessing sensitive data in the destination country. Since 2021, SCCs have required companies to include detailed descriptions of their technical and organizational security measures, with access governance being a critical component.
Effectiveness in Reducing Cross-Border Risks
RBAC and MFA address surveillance concerns by restricting access to sensitive data strictly to defined roles and requiring identity verification for every access attempt. A growing trend is the implementation of "Access Justifications", where users must provide a valid reason for accessing sensitive data or encryption keys. This not only strengthens security but also creates a detailed audit trail for regulators. Additionally, systems can be designed so that foreign teams handle only pseudonymized or tokenized datasets, ensuring they access only the data attributes necessary for their tasks.
Ease of Implementation and Scalability
Modern cloud platforms simplify the deployment of RBAC and MFA with automated tools - such as pre-configured blueprints - that establish baseline access controls and enforce MFA for compliance. To scale these safeguards, organizations should mandate MFA for all user accounts with access to sensitive data, especially in regions without adequacy decisions. Regular audits of service accounts can help identify and address over-privileged access, reducing the risk of unintended data exposure during cross-border transfers. Tools like Security Command Center can monitor and flag noncompliance issues, such as over-privileged accounts, in real time.
3. Geo-Fencing and Conditional Access Policies
Geo-fencing and conditional access policies play a crucial role in controlling data operations based on geography and device security. These measures are increasingly important as countries enforce strict local data handling laws. For instance, Russia's Federal Law No. 242-FZ mandates that personal data of Russian citizens must be stored and processed on servers within Russia's borders. Similarly, China's Cybersecurity Law requires critical infrastructure operators to store data locally. These policies set the stage for a broader discussion on enforcement strategies.
Data Protection and Security
Geo-fencing enhances data protection by restricting access and transfers to specific geographic zones, ensuring data remains within authorized regions. Tools like Attribute-Based Access Control (ABAC) add another layer of security by using real-time factors - such as GPS location or device security status - to enforce context-aware access. Cloud platforms can automatically block or reroute data transfers that violate regional restrictions. Additionally, VPC Service Controls help minimize the risk of unauthorized data transfers or copying. As DataProbity explains:
"Data sovereignty isn't just a compliance requirement. It's a design principle for operationalizing privacy in a global landscape."
Compliance with Global Regulations
These geographic controls are essential for demonstrating compliance with international regulations. For example, under GDPR, remote access to data from a third country - even for IT support - qualifies as a cross-border data transfer. The €1.2 billion fine imposed on Meta Platforms Ireland highlights the importance of robust geographic controls in managing such transfers.
To meet these requirements, organizations can adopt operational sovereignty measures, such as limiting data access based on personnel attributes like citizenship or physical location. Tools like Google Cloud's Assured Workloads automate this process by establishing baseline access controls and data location restrictions tailored to compliance frameworks like FedRAMP or CJIS. Documenting these geographic controls also supports Transfer Impact Assessment (TIA) requirements, a key focus following the Schrems II ruling.
Ease of Implementation and Scalability
Modern cloud platforms have made it easier to enforce these policies through automation. Tools like AWS Config Rules, Azure Policy, and Google Cloud organization policies can automatically enforce data residency requirements and restrict resource creation to specific regions. Sensitive data can also be tagged with metadata that specifies jurisdictional restrictions, allowing machine learning tools to dynamically enforce residency rules. Additionally, implementing IAM policies that require multi-factor authentication and device health checks adds another layer of security for cross-border access. These automated solutions help organizations maintain compliance as they expand into multiple jurisdictions, reducing the risk of oversight.
4. Logging and SIEM Monitoring
Building on encryption and access controls, logging and Security Information and Event Management (SIEM) monitoring play a crucial role in security by creating detailed audit trails for cross-border data movements. These systems track who accessed data, when, and from where - turning compliance into actionable, verifiable records.
Data Protection and Security
Centralized logging acts as what Jim Kutz from Airbyte describes as a "living inventory of data hops". This level of visibility is essential for spotting and addressing unauthorized access before it becomes a larger issue. SIEM tools take it a step further by monitoring for data exfiltration attempts and sending alerts for unauthorized copying or transfers. Many modern cloud platforms also include Access Transparency features, offering near real-time logs of administrator access to customer data. As Google Cloud explains:
"Our audit logs provide you with near real-time logs of Google administrator access on Google Cloud."
These tools not only enhance security but also help mitigate insider threats by providing transparency and accountability.
Compliance with Global Regulations
Global regulations like GDPR require that every cross-border data transfer is traceable to its legal basis, whether through Standard Contractual Clauses, Binding Corporate Rules, or adequacy decisions. By tagging synchronization metadata with specific "GDPR tags" and streaming it into SIEM systems, organizations can maintain compliance at scale. The stakes for non-compliance are high - violations can lead to fines of up to €20 million or 4% of global annual turnover. For instance, in April 2023, Meta Platforms Ireland faced a €1.2 billion fine from the Irish Data Protection Commission for transferring data to the U.S. without sufficient safeguards.
Other regulations, like the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA), add further urgency. Covered entities must report cyber incidents within 72 hours and ransomware payments within 24 hours. These logging practices, when combined with technical safeguards, create a robust framework for cross-border data security.
Effectiveness in Reducing Cross-Border Risks
Unified logging transforms compliance from a reactive obligation to an active risk management tool. With a centralized dashboard, organizations can instantly show where data moved and what safeguards were applied. This is critical because even something as simple as remote IT support from another country can qualify as a cross-border transfer under GDPR. Centralized audit trails also allow organizations to revoke credentials across all operations globally, avoiding slow, region-by-region fixes.
Additionally, tools like VPC Flow Logs and Firewall Rules Logging automatically record network traffic, providing both evidence for regulatory audits and a way to detect unauthorized network activity.
Ease of Implementation and Scalability
Cloud-native monitoring tools make implementation straightforward. For example, VPC Flow Logs automatically track network traffic to and from virtual machine instances, while Firewall Rules Logging monitors TCP/UDP connections within virtual private clouds. Separating the control plane from the data plane further centralizes log visibility while ensuring personal data stays within designated jurisdictions. For workloads in the EU, adopting an outbound-only communication model - where systems push updates via outbound TLS connections and block all inbound firewall ports - reduces the risk of unauthorized external access.
5. Data Minimization and Anonymization Techniques
Does every piece of data truly need to cross borders? By using data minimization and anonymization techniques, organizations can limit the amount of sensitive data transferred, reducing risks and bolstering existing safeguards.
Data Protection and Security
One powerful tool in this area is pseudonymization. This process alters data so it cannot be linked to a specific individual without additional information - like cryptographic keys or re-identification algorithms. The key to its effectiveness lies in ensuring that this additional information is kept solely by the data exporter and stored within the EEA or another jurisdiction deemed adequate. As the European Data Protection Board (EDPB) highlights:
"Pseudonymization also can serve as an effective supplementary measure... especially where a data exporter pseudonymizes data prior to the transfer [and] any additional data is held exclusively by the data exporter."
For even greater protection, split processing divides personal data among multiple independent importers in different jurisdictions. This ensures that no single party has access to enough information to reconstruct the original dataset, significantly reducing the risk of unauthorized access.
Compliance with Global Regulations
Under the GDPR, data minimization is a key principle that applies to every international transfer. The EDPB stresses:
"When transferring personal data, you still need to make sure that... you only process the personal data necessary for this particular processing activity (principle of data minimisation)."
This means organizations must evaluate the necessity of every data field they process. This becomes even more critical when considering that over 60 countries enforce specific data transfer rules and that 90% of global data is unstructured.
Effectiveness in Reducing Cross-Border Risks
These techniques do more than ensure compliance - they also reduce an organization’s vulnerability to data breaches. Properly implemented pseudonymization, for instance, ensures that even if data is intercepted, it cannot be linked back to individuals. For this to work, the re-identification keys must remain exclusively under the control of the data exporter and never shared with importers in non-adequate countries.
Additionally, combining pseudonymization with strict access policies - such as limiting access to authorized personnel only - can further protect transferred data. However, achieving these benefits requires meticulous planning and execution.
Ease of Implementation and Scalability
While effective, these techniques can be challenging to implement. For example, split processing involves coordinating multiple independent processors across different jurisdictions, which can be complex and resource-intensive.
| Technique | Risk Mitigation | Implementation Complexity |
|---|---|---|
| Pseudonymization | High; prevents re-identification if keys are retained within the EEA | Moderate to High; requires robust key management |
| Split Processing | Very High; no single entity has a complete dataset | High; requires coordinating multiple independent processors |
| Data Minimization | Foundational; reduces the overall volume of data exposed to risk | Moderate; requires ongoing process audits |
To streamline these efforts, organizations should map non-EEA data flows and conduct Transfer Impact Assessments (TIA) to identify which techniques are necessary. Modern data intelligence tools can further simplify this process by automating data mapping and classification tasks, making these safeguards more scalable.
Conclusion
Protecting global data transfers isn't just a best practice - it's a legal necessity. Companies that fail to implement proper technical safeguards risk hefty penalties, including fines of up to €20 million or 4% of their global annual turnover. Nicola McCrudden, Of Counsel at Ogletree Deakins, puts it plainly:
"Noncompliance with the EU GDPR and UK GDPR can attract regulatory fines of up to 4 percent of an organization's global annual turnover."
The five key safeguards - encryption, RBAC with MFA, geo-fencing, logging with SIEM, and data minimization or anonymization - work together to address risks highlighted by Transfer Impact Assessments (TIAs). These measures aim to protect personal data from unauthorized access by foreign governments or surveillance authorities in third countries. Since the Schrems II ruling, regulators have intensified their scrutiny, examining both private companies and public institutions for compliance with cross-border data transfer rules.
To stay compliant, organizations should map all data transfers, including remote access from outside the EEA, and conduct TIAs for any transfers not covered by adequacy decisions. When using encryption or pseudonymization, ensure that encryption keys remain within the EEA or another secure jurisdiction. This prevents foreign authorities from accessing sensitive data and ensures that transferred information cannot be linked back to specific individuals.
As laws and technologies continue to evolve, it's critical to reassess your safeguards regularly. Verify the legal framework of each destination country to ensure ongoing compliance and effectiveness. With 88% of organizations relying on Standard Contractual Clauses as their primary transfer mechanism, implementing strong supplementary measures is more important than ever to protect data and maintain secure global operations. These actions are essential for navigating the complexities of international data transfers while staying on the right side of the law.
FAQs
Do remote employees overseas count as a data transfer?
Yes, hiring remote workers in other countries does count as a data transfer. When you share personal or sensitive information across borders, you're moving data outside your local jurisdiction. This activates cross-border data transfer rules, meaning you’ll need to put the right safeguards in place to stay compliant and keep that data secure.
What is a Transfer Impact Assessment (TIA) and when do I need one?
A Transfer Impact Assessment (TIA) examines the risks and legal considerations involved in transferring personal data from the European Economic Area (EEA) to countries outside the European Union. Its purpose is to ensure compliance with GDPR requirements and determine whether extra safeguards are necessary. TIAs are particularly important when relying on mechanisms like Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs) for data transfers to countries that lack an EU adequacy decision. This process helps address and reduce potential risks to data protection.
Where should encryption keys be stored for cross-border compliance?
Encryption keys need to be handled with care to ensure data security. It's best to store them in a secure system that you either own or have full control over. Keeping them separate from the data they protect is crucial. This approach not only enhances security but also helps meet regulations for cross-border data transfers.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)