How Third-Party Integrations Impact Consent Flows

When you click "Accept" on a website, you might unknowingly allow hundreds of third-party tools to access your data. These integrations are growing fast - by 123% year-over-year - but they come with risks. In 2024, 35.5% of data breaches were linked to third-party vulnerabilities. Managing consent in this environment is tough, especially with regulations like GDPR requiring explicit consent and CCPA focusing on opt-out rights.
Key challenges include:
- Complex multi-step consent flows: Each integration needs separate consent tracking.
- Vulnerabilities: OAuth tokens and shadow integrations can bypass security.
- Compliance gaps: 94.1% of consent forms fail to fully respect user preferences.
Tools like AI-powered synchronization, consent APIs, and real-time updates can help businesses stay compliant while protecting user data.
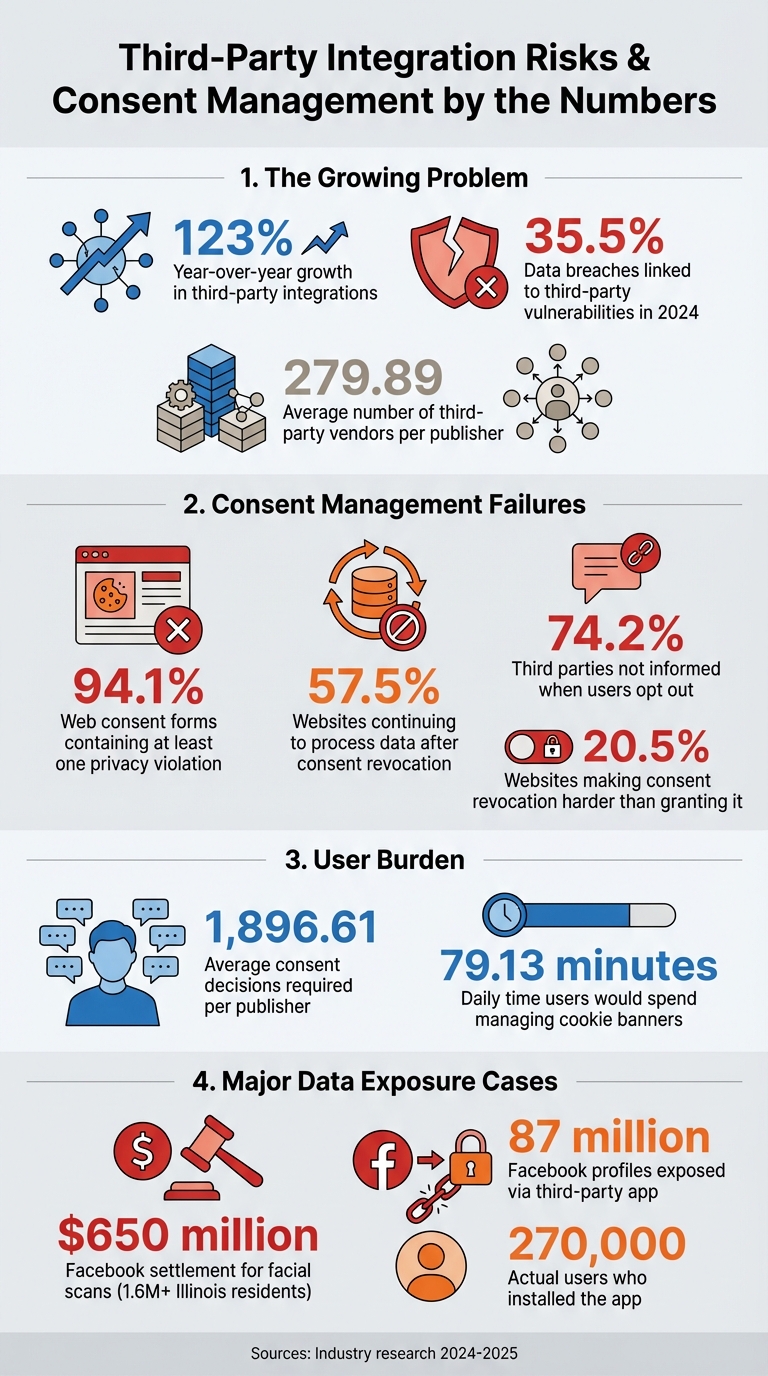
Third-Party Integration Risks and Consent Management Statistics 2024-2025
Research on Third-Party Integration Risks
Data Sharing Risks in Multi-Vendor Systems
Recent research highlights the vulnerabilities tied to data handling in multi-vendor systems. In April 2025, a team from Inria and Utrecht University examined 718 tags within Google Tag Manager and uncovered widespread privacy issues. These tags often set cookies and shared personal data with third parties - violating their own legal claims.
Even with the introduction of Google Consent Mode v2 in March 2024, privacy concerns persist. This updated system sends "cookieless pings" to Google's servers, communicating user activity and consent states - even when users explicitly deny consent. Researcher Gilles Mertens clarifies:
"Data is actively collected via 'cookieless pings' despite being declared as passively sent and despite user's consent refusal".
Another layer of risk comes from interdependent privacy (IDP), where one user's data-sharing actions expose others who haven't consented. Facebook's 2021 settlement is a striking example. The company paid $650 million to over 1.6 million Illinois residents for creating facial scans without their permission, using photo-tagging features. Similarly, the "thisisyourdigitallife" app harvested data from 87 million Facebook profiles, even though only 270,000 users had installed the app.
These technical and systemic vulnerabilities point to larger compliance issues, which are explored further in the next section.
Compliance Gaps in Consent Management
The technical risks of data sharing are compounded by compliance failures in consent management. Research shows that Consent Management Platforms (CMPs) often fall short of enforcing user preferences. For instance, a study revealed that 94.1% of web consent forms contain at least one privacy violation, such as failing to provide withdrawal options or using vague purpose descriptions. Even when users revoke consent, 57.5% of websites continue processing data through cookies.
A major issue lies in the lack of communication between CMPs and third-party vendors. When users opt out, 74.2% of third parties that previously received consent signals are not informed about the revocation. As a result, these third parties continue collecting data as if consent was still in place. Moreover, 20.5% of websites make it harder for users to revoke consent than to grant it - often requiring navigation through footer links, privacy policies, or multi-step settings, while acceptance is just a simple click.
sbb-itb-5f36581
GDPR vs. CCPA: How Third-Party Integrations Affect Compliance
GDPR: Explicit Consent and Renewal Requirements
GDPR follows a strict opt-in model, meaning businesses must secure clear and explicit permission before any third-party tool can process personal data. This creates a unique challenge for managing integrations, especially considering that the average publisher works with 279.89 third-party vendors. To fully comply, users would need to make decisions for each vendor's specific purposes - resulting in an overwhelming 1,896.61 decisions per publisher on average.
If users were to handle all these granular decisions, they would spend around 79.13 minutes daily managing cookie banners. This overwhelming burden often leads users to click "accept all", which undermines the intent of the regulation.
Additionally, GDPR mandates periodic consent renewal. The UK Information Commissioner's Office (ICO) advises businesses to seek fresh consent for storage and access technologies every 6 months. Celestine Bahr, Director Legal, Compliance & Data Privacy at Usercentrics, emphasizes:
"The GDPR generally requires opt-in consent, meaning businesses need clear permission before processing most types of personal data".
| Feature | GDPR Requirements | CCPA/CPRA Requirements |
|---|---|---|
| Primary Model | Opt-in (prior consent required) | Opt-out (right to say "no" to sale/sharing) |
| Third-Party Disclosure | Must list specific identities of third parties | Must describe categories of third parties and provide opt-out links |
| Re-solicitation | Recommended every 6 months | Must wait 12 months after an opt-out |
| Role Definitions | Controller and Processor | Business, Service Provider, and Third Party |
These differences underline the intricate compliance challenges publishers face when managing third-party integrations.
CCPA: Opt-Out Rights and User Control
Unlike GDPR's opt-in model, CCPA operates on a default data collection approach, with clear opt-out mechanisms for personal information sale or sharing. This makes compliance with third-party integrations a different kind of challenge.
Under CCPA, businesses must classify each integration as either a "Service Provider" (processing data solely for the business) or a "Third Party" (using data for their purposes). Tanya Forsheit, Vice President and Chief Privacy Officer at The New York Times Company, comments on the complexity:
"That new ecosystem bears little resemblance to the controller/processor structure of the EU General Data Protection Regulation and leaves much to be desired when it comes to facilitating the privacy practitioner's job of categorizing and risk-ranking business partners".
The regulation also enforces strict re-solicitation rules. If a consumer opts out of data selling or sharing, businesses must wait at least 12 months before requesting them to opt-in again. Additionally, websites must respect universal opt-out signals, such as Global Privacy Control (GPC), which automatically applies user preferences across all third-party integrations. Lothar Determann, a contributor to IAPP, highlights:
"Opt-in banners optimized for compliance with the GDPR are not ideal for California and likely even violate CCPA".
Tools and Methods for Better Consent Flow Management
AI-Powered Consent Synchronization
Managing consent across multiple vendors can be a logistical nightmare, but AI is stepping in to simplify the process. Take Securiti, for example - it uses AI to automatically gather, organize, and synchronize consent data across thousands of integrations in cloud and SaaS environments. This automation eliminates the need for manually tracking consent statuses for every third-party tool, saving time and reducing errors.
Platforms like MetaRouter ACE go a step further by enforcing consent server-side. This ensures that data doesn’t reach third-party APIs without proper authorization, even if a user's browser has been compromised. Additionally, tools now adhere to Google Consent Mode v2, which is essential for managing ad-based consent signaling.
Cryptographic verification is another safeguard gaining traction. Didomi’s "Didomi Signature" secures consent strings with cryptographic protection during data transfers. Jeff Wheeler, VP of Product at Didomi, describes its purpose:
"We built DCS and Signature to give our customers what the industry was missing: a simple, verifiable way to prove consent integrity without slowing anything down".
Their Didomi Consent String (DCS) compresses consent data into a lightweight binary format under 2KB, which avoids cookie bloat and helps maintain SEO performance.
Real-time synchronization is also critical. Plaid’s Permissions Manager uses webhooks like permission_revoked, ensuring that user opt-outs on one platform are instantly applied across all connected apps and third-party tools. Without this synchronization, apps could mistakenly show active connections after access has been revoked, leading to compliance risks and user frustration.
These advanced tools and safeguards make consent management more reliable and efficient, but mapping consent flows effectively is just as important.
How Reform Supports Consent Flow Mapping
Reform offers features designed to simplify consent flow mapping. Its conditional routing automatically directs users to the appropriate consent flows based on their location or the type of data being collected. For instance, users under GDPR rules will see opt-in prompts, while those governed by CCPA will encounter opt-out mechanisms - all without requiring manual adjustments.
The platform also provides real-time analytics to monitor consent rates and pinpoint where users drop off. This creates an audit trail essential for regulatory compliance and helps businesses fine-tune their consent processes. Combined with lead enrichment tools, Reform ensures businesses collect necessary data while staying firmly within compliance boundaries.
Here’s a breakdown of Reform’s pricing and features:
| Reform Plan | Price | Consent Flow Features | Integration Support |
|---|---|---|---|
| Basic | $15/mo or $150/yr | Conditional logic, custom thank-you pages, headless forms | Notion, Google Sheets, Zapier, ConvertKit |
| Pro | $35/mo or $350/yr | Team access, incomplete response tracking, custom CSS/JS | Everything in Basic + HubSpot (Salesforce coming soon) |
| Done for You | Custom | Fully customized consent flows designed by experts | Tailored to specific compliance needs |
On the technical side, Reform leverages ISO 27001 encryption (TLS 1.3/AES-256) to secure data during transfers. Its webhook capabilities also support events like permission_granted and permission_revoked, ensuring internal authorization records stay in sync with user actions across various systems.
What is a Consent Management Platform (CMP)?
Conclusion: Managing Consent with Third-Party Integrations
Using a Consent Management Platform (CMP) as a centralized hub for tracking consent simplifies the process and minimizes the risk of regulatory issues. By acting as a single source of truth, it removes the hassle of manually managing permissions across various vendors.
Adopting granular, purpose-specific consent practices - like separating analytics from marketing - helps build user trust and ensures clarity. A great example of this is Microsoft Clarity's Consent API V2, which allows independent consent signals for analytics_Storage and ad_Storage. This ensures that cookies are only set when the appropriate permissions are granted.
These advanced controls work seamlessly with continuous monitoring tools, which help maintain compliance throughout the consent lifecycle. Automated systems can detect and address issues before they escalate. As Secure Privacy emphasizes:
"Third-party risk management for consent isn't merely a compliance function - it's a fundamental component of responsible data stewardship and customer relationship management in today's privacy-conscious world".
In a landscape where privacy expectations are high, tools like Reform simplify consent mapping with features such as conditional routing that adapts based on user location. Real-time analytics further enhance the process by tracking consent rates and identifying where users drop off. Reform also offers strong security measures and real-time synchronization, making compliance more manageable.
Together, these strategies highlight the importance of robust technical safeguards, transparent communication with users, and automation to handle the complexities of third-party consent management effectively.
FAQs
How can I tell which integrations are collecting data before a user consents?
Auditing third-party data practices is crucial to spot integrations that might collect data before obtaining user consent. Many tracking libraries rely on developers to handle consent management, which means they could begin gathering data even before users give their approval. By carefully reviewing these practices, you can ensure compliance and create a smoother, more transparent consent process.
What’s the safest way to sync consent changes across all third parties in real time?
The safest way to keep consent changes aligned across all third-party platforms in real time is through webhooks or API-based two-way synchronization. Tools like iubenda’s 2-Way Sync make this process seamless by automatically updating consent statuses across platforms, ensuring both compliance and accurate data handling.
How do I design one consent flow that works for both GDPR and CCPA?
When creating a consent flow that aligns with both GDPR and CCPA, it's essential to prioritize clarity and user control. These two regulations have distinct requirements, so your design must cater to both.
Under GDPR, users must provide explicit opt-in consent. This means you need to present clear options, such as "Accept" and "Reject", ensuring users actively agree to data collection. On the other hand, CCPA operates with an opt-out model by default. It requires you to include a visible and straightforward "Do Not Sell My Personal Information" option.
To simplify compliance and improve user experience, consider implementing a centralized consent management system. This system can help you efficiently manage and synchronize user preferences across different regions, ensuring adherence to both GDPR and CCPA requirements without overwhelming users.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)