Best Practices for Vendor Data Sharing Compliance

When sharing customer data with vendors, you’re not just handing over data - you’re also sharing legal responsibility. Noncompliance with GDPR or CCPA can lead to steep fines: up to 4% of annual revenue for GDPR violations or $7,500 per intentional violation under CCPA. Here’s how to stay compliant:
- Vendor Due Diligence: Assess vendors’ security practices, certifications, and breach history. Build an inventory of all vendors handling customer data and prioritize based on risk.
- Contracts and Agreements: Always sign a Data Processing Agreement (DPA) with vendors. Specify data usage, security measures, breach notification timelines, and audit rights in contracts.
- Security Measures: Enforce encryption (AES-256), multi-factor authentication, and role-based access controls. Monitor vendor data access in real time and conduct regular security audits.
- Consent Management: Collect and document explicit user consent when required. Use tools to log consent records and ensure compliance with GDPR and CCPA opt-in/opt-out models.
- Ongoing Monitoring: Schedule regular vendor audits and track compliance. Address issues immediately and terminate relationships if standards aren’t met.
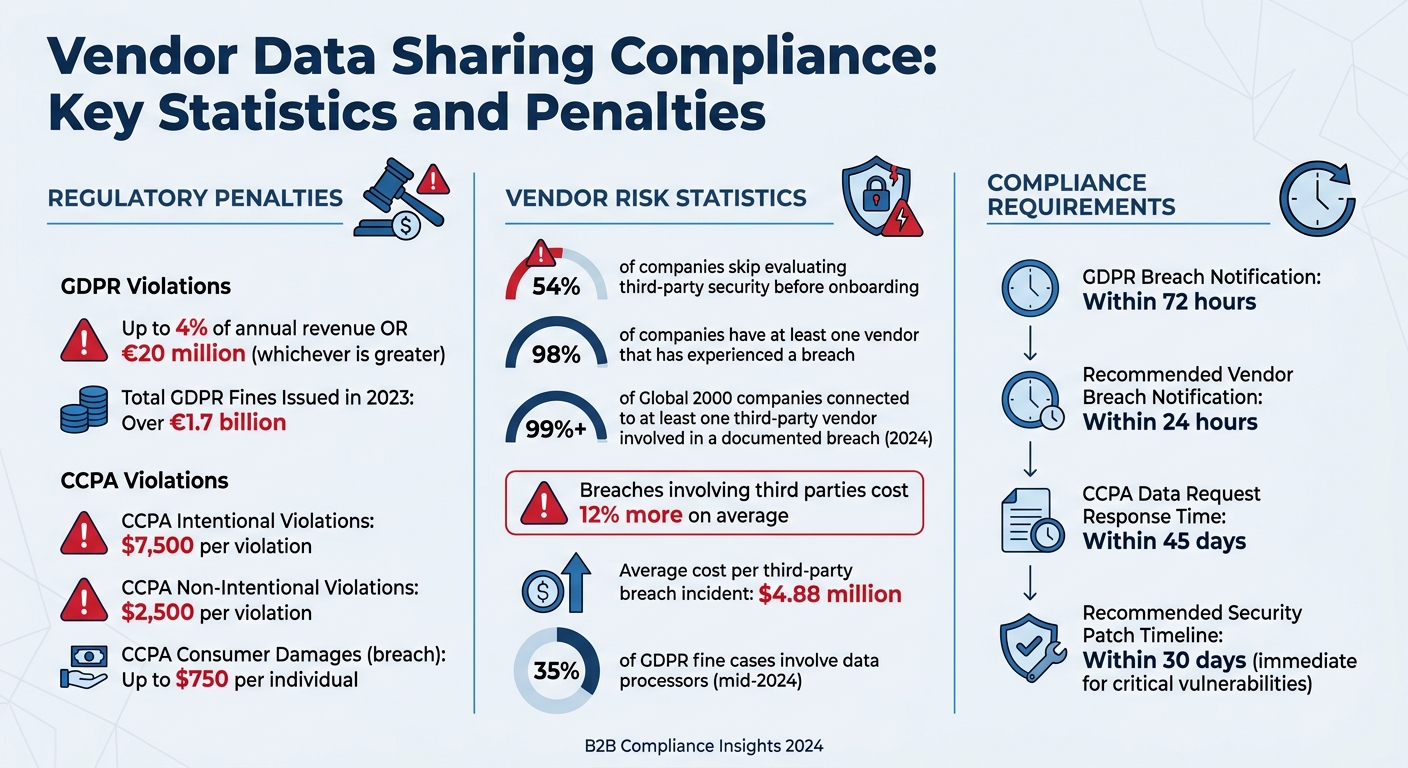
Vendor Data Sharing Compliance: Key Statistics and Penalties
Managing GDPR Vendor Third Party Risk Management Across Supply Chain
sbb-itb-5f36581
Conducting Vendor Due Diligence
With the increasing occurrence of data breaches, taking a close look at your vendors is no longer optional - it's a necessity. Before handing over any customer data, make sure your vendors have solid data-handling practices. Recent stats reveal some concerning trends: 54% of companies skip evaluating third-party security before onboarding, 98% have at least one vendor that has experienced a breach, and breaches involving third parties tend to cost 12% more - averaging a hefty $4.88 million per incident.
"The GDPR is explicit: ignorance of what your processors do is not a defence." – Custodia Privacy
Start by building a full inventory of all vendors that interact with customer data. This includes SaaS tools, APIs, payment processors, and analytics platforms. Categorize each vendor based on the type of data they handle, such as personal identifiers, sensitive data, or anonymized information. This inventory doubles as your Record of Processing Activities (ROPA), a GDPR requirement. Once you have this foundation, you can prioritize vendors based on risk and decide how deeply to scrutinize each one.
Not all vendors pose the same risk. For instance, critical vendors like CRMs or payment processors demand detailed reviews, including questionnaires with over 150 questions and a thorough policy check. On the other hand, standard vendors might only need a quick review of certifications and a shorter questionnaire.
Keep an eye out for ambiguous language in vendor privacy policies. Phrases like "we may share data with partners" or "we use data to improve our products" could mean the vendor is acting as a joint controller, not just a processor. This distinction can require a more complex Article 26 agreement under GDPR. Also, be cautious of vague data retention policies, such as "as long as necessary for business purposes", which lack clear timeframes and should raise a red flag.
Review Vendor Policies and Certifications
Under GDPR Article 28, any vendor handling personal data must sign a Data Processing Agreement (DPA). This document outlines what data is processed, how it’s secured, and your audit rights. Without a DPA in place, you're exposing your organization to compliance risks.
"A single un-DPA'd vendor processing EU personal data puts your entire compliance posture at risk." – Custodia Privacy
Check where your data will be stored. If a U.S.-based vendor processes EU customer data, confirm they’re listed under the EU–US Data Privacy Framework (DPF). If not, ensure they use Standard Contractual Clauses (SCCs) or UK International Data Transfer Agreements (IDTAs) to comply with data transfer rules.
Security certifications like ISO 27001 or SOC 2 Type II can indicate strong security measures and help you assess whether the vendor meets GDPR’s "sufficient guarantees" requirement. Always request full audit reports, not just certification logos. For SOC 2 reports, focus on the "exceptions and deficiencies" section to understand how any issues were addressed.
Ask for the vendor’s list of sub-processors. You’re responsible for the entire chain of accountability, so an outdated list (not updated in the past 18 months) should raise concerns. Also, review the vendor’s breach history and notification process. GDPR requires vendors to notify you of a breach without undue delay, ideally within 72 hours, so make sure they have a documented notification timeline.
Once you’ve reviewed policies and certifications, confirm that the vendor’s real-world security practices align with what they’ve promised.
Verify Data Security Practices
Certifications are a good starting point, but you need to dig deeper into the vendor’s actual security measures. Ensure they use AES-256 encryption for data at rest, TLS 1.2+ for data in transit, multi-factor authentication (MFA), and role-based access control (RBAC) with regular audits. These are baseline measures for compliance with GDPR and CCPA. Verify that only authorized personnel can access customer data and that access is logged and audited regularly.
Check if the vendor conducts regular security tests. Annual penetration testing and quarterly vulnerability scans by independent third parties are highly recommended. Ask for summaries of these tests and inquire about their process for patching vulnerabilities.
For ongoing monitoring, consider using security rating tools like BitSight or SecurityScorecard. These services provide real-time insights into a vendor’s security posture.
Finally, confirm that the vendor can handle Data Subject Access Requests (DSARs). They should have systems in place to manage requests for data access, erasure, or portability within the required timeframes. Testing their DSAR process during onboarding can reveal their readiness.
Keep detailed records of each vendor, including their DPA status, data transfer mechanisms, certification expiry dates, and the date of your last assessment. Set reminders to review certifications and performance at least 90 days before contract renewals. Regular reviews can also help you identify "zombie tools" - vendors that still have access to live data even though they’re no longer in active use.
Adding Compliance Clauses to Vendor Contracts
Once you've thoroughly evaluated your vendors, the next step is to solidify expectations in writing. A strong contract does more than just outline services - it builds a legal framework that shields your business from regulatory penalties and reputational harm. For context, regulators issued over €1.7 billion in GDPR fines in 2023 alone, with data processors found responsible for 35% of GDPR fine cases by mid-2024 due to weak security measures in their agreements. Clearly, vague promises or generic contract language won't cut it.
Your vendor contracts should leave no room for ambiguity. They need to spell out how data will be managed, who is responsible when issues arise, and the consequences of failing to meet obligations. Contracts should translate your due diligence findings into enforceable commitments. For instance, enforcing a simple "30-day rule" - where vendors gain data access only after signing a Data Processing Agreement (DPA) - can prevent unauthorized exposure and set a firm legal foundation for the relationship.
Required Elements in Data Processing Agreements
A Data Processing Agreement (DPA) is critical for compliance with laws like GDPR and CCPA. It ensures that vendors only act on your written instructions and prohibits them from misusing customer data. The agreement must clearly define the scope of data processing, including its purpose, duration, and the types of personal data involved, as well as the categories of individuals affected. Without this clarity, you risk vendors mishandling your data.
Your DPA should also go beyond the minimum legal requirements for breach notifications. While GDPR allows up to 72 hours for reporting, you can require vendors to notify you within 24 hours. This gives you extra time to assess the situation and comply with reporting deadlines. The agreement should specify what details the vendor must provide in the event of a breach, such as the type of data affected, the number of people impacted, and preliminary findings about the cause.
"A strong DPA ensures that your analytics tools, ad platforms, and cloud services are all aligned with your company's data governance standards, preventing unauthorized data use and protecting your brand's reputation." – Trackingplan
Additionally, vendors must obtain written consent before involving sub-processors and impose the same data protection obligations on them. Your contract should also include audit and inspection rights, allowing you to verify compliance through audits or documentation.
Another essential element is assistance with Data Subject Access Requests (DSARs). The DPA should specify how vendors will help you meet deadlines for data access, deletion, or portability requests. Finally, the agreement must require vendors to delete or return all personal data once the service ends, ensuring sensitive information isn't stored indefinitely.
Under CCPA and CPRA, these clauses help prevent the sharing of personal information from being legally classified as a "sale" or "sharing", which would otherwise trigger consumer opt-out rights. Including a certification clause is also wise - vendors should confirm in writing that they understand and will comply with your data restrictions.
By establishing these standards, you create a strong foundation for data protection and compliance.
Specifying Security and Access Requirements
Avoid vague terms like "reasonable security measures" in your contracts. Instead, set clear technical standards. For example, require TLS 1.3+ for data in transit, AES-256 encryption for data at rest, multi-factor authentication (MFA), and role-based access controls.
"A vendor's hesitation to detail their security protocols in the data process agreement is a clear warning sign. Transparency here is not optional - it's a direct reflection of their commitment to protecting your most valuable asset." – Trackingplan
Your contracts should also define vulnerability management expectations. Require vendors to apply security patches within 30 days - or immediately for critical vulnerabilities. Include rights for annual penetration testing and on-site audits, and insist on independent verification through SOC 2 Type II reports or ISO 27001 certifications.
To ensure compliance across the supply chain, include cascading clauses that require vendors to impose the same security obligations on their subcontractors. For critical vendors, demand cyber liability insurance with minimum coverage of $1 million to $5 million, depending on their role, and request to be named as an "additional insured" on their policies.
If your data will be transferred internationally - such as to the European Economic Area or the UK - include Standard Contractual Clauses (SCCs) as a mandatory appendix. Post-Brexit, data transfers from the UK require a specific "UK Addendum" alongside the EU SCCs to maintain compliance. These measures provide a legal basis for international data transfers and protect your business from regulatory scrutiny.
Setting Up Security Measures for Data Sharing
Once vendor agreements are finalized, technical controls become the backbone of enforcing the security standards outlined in those contracts. Without solid technical measures, even the best-written agreements fall short. Regulatory frameworks like GDPR Article 32 and CCPA Section 1798.150 emphasize the importance of implementing security protocols that match the level of risk. Core measures like encryption and access controls are non-negotiable and should be central to your security strategy. Always operate under the assumption that any vendor could be compromised, and build your defenses accordingly.
Apply Zero-Trust Security Principles
Zero-trust security practices are essential to putting these controls into action. The philosophy is straightforward: never trust, always verify. No vendor or subcontractor, regardless of their reputation or agreements, should have automatic access to your data. Every access attempt must be authenticated, authorized, and monitored.
Start by implementing multi-factor authentication (MFA) for all vendor accounts accessing your systems. Pair this with role-based access control (RBAC) to ensure users can only access data relevant to their specific roles. For instance, a marketing analytics vendor should have access to campaign performance data but not sensitive customer payment details. For programmatic access, use API token authentication, ensuring tokens have expiration dates and can be revoked immediately when necessary.
"Sovereignty is maintained not because the vendor has made appropriate promises, but because the vendor has no technical capability to violate them." – Kiteworks
Data minimization is another critical step. Share only the minimum amount of personally identifiable information (PII) needed for each task. If full datasets aren't necessary, use techniques like masking or anonymization. Clearly label each PII field in your data catalog with its intended purpose to avoid misuse. Additionally, use customer-owned encryption keys so that even if vendors are compelled by legal requests, such as those under the U.S. CLOUD Act, they cannot decrypt your data.
Track Data Access and Activity in Real-Time
Zero-trust measures should be paired with continuous, detailed monitoring. Real-time tracking of data access and activity is crucial for compliance with GDPR and CCPA. Use SIEM systems to log every interaction - who accessed the data, when, what actions were performed, and from which location. Set up alerts for unusual patterns, such as large data downloads during off-hours or access from unexpected regions.
Ensure your logging system creates immutable audit trails that cannot be tampered with, even by administrators. Maintain data lineage records that trace the flow of data from its collection and processing to its eventual deletion. Automate permissions management at a granular level - whether by workspace, table, or specific columns - based on predefined roles. If a vendor employee leaves or changes roles, their access should be terminated immediately to prevent lingering permissions. Regularly reviewing access logs can help identify dormant accounts or users with excessive privileges.
Keep in mind that encryption by itself isn’t a silver bullet. Always store encryption keys separately from the encrypted data. If both are compromised during a breach, your organization could lose notification exemptions under California law, exposing you to disclosure requirements and potential civil damages of up to $750 per affected consumer.
Monitoring and Auditing Vendors
Strong security measures are a good starting point, but they’re not enough on their own. Regular audits are essential to ensure vendors maintain compliance over time. In 2024, more than 99% of Global 2000 companies were connected to at least one third-party vendor involved in a documented breach. Interestingly, most GDPR enforcement actions stem from poor vendor oversight rather than internal control issues. Without audits, relying purely on trust becomes a risky gamble, especially with steep regulatory penalties in play.
Set Up Regular Audit Schedules
Once your security measures are in place, regular audits can help ensure vendors stick to compliance standards. The frequency of audits should depend on the type of data a vendor handles, not just their size. For instance, even a small SaaS tool can pose a high risk if it processes sensitive data like identity information, behavioral patterns, or confidential records. Vendors managing high-risk data - such as biometrics, financial details, or healthcare information - should be audited annually or biannually. On the other hand, vendors dealing with less critical data, like basic contact information, can be reviewed less often, but no less than once every two years.
To make this process smoother, include audit rights in your Data Processing Agreements (DPAs). These agreements should clearly state your right to conduct both scheduled and unscheduled audits, especially when new risks emerge. They should also require vendors to notify you of any breaches within 24–48 hours, which could then trigger an immediate audit. Standardized audit questionnaires can help speed up onboarding and simplify routine reviews.
In addition to scheduled audits, continuous monitoring is key. Set up real-time alerts for unusual activity, such as unexpected data access or changes in a vendor’s security posture. Regularly review vendor logs to track access to sensitive information and ensure all changes are properly recorded. Companies like Checkr have seen significant benefits from automation - cutting vendor review times by 80% using Auditive’s AI-driven workflows - while PayNearMe saved over 425 hours annually by moving away from manual processes to centralized monitoring. These practices ensure you're ready to act quickly when problems arise.
Address Audit Findings
If an audit reveals non-compliance, it’s important to act immediately. Start by identifying which data or processes are affected. Then, work with the vendor to determine the root cause and set clear deadlines for corrective actions. If human error is to blame, require retraining for their staff who handle sensitive data.
Vendors may need to update their technical controls, improve internal policies, or revise documentation. Use automated tools to track their progress and confirm that changes are properly implemented. For vendors with recurring issues, increase the frequency of audits and boost real-time monitoring until they meet compliance standards. Keep detailed records of the root causes and corrective actions for internal reporting or regulatory purposes. If a vendor fails to improve or meet your standards, it may be time to switch providers or bring the work in-house. Before ending the relationship, ensure all data is either securely returned or deleted.
Using Reform for Consent Management
After conducting thorough vendor audits, managing user consent becomes a crucial step in maintaining compliance. It's essential to obtain explicit, documented consent before sharing any data with third parties. Under GDPR, organizations are required to establish and document a lawful basis for data sharing to meet the accountability principle. Similarly, the CCPA mandates that businesses provide a clear and accessible notice to consumers at or before data collection. This notice must outline the categories of information being collected and how it will be used. Ignoring proper consent capture and storage can result in penalties under both GDPR and CCPA.
Build Consent Forms Without Code
Reform's no-code form builder makes creating compliant consent forms simple and efficient. You can design multi-step forms that break down consent requests into smaller, more understandable sections, such as contact details, data-sharing preferences, and vendor-specific consents. With conditional routing, you can customize the user experience by showing or hiding certain options based on their responses. For example, if a user indicates they are under 16, the form can automatically enforce explicit opt-in requirements for processing sensitive data.
Reform also includes email validation and spam prevention tools to ensure you capture only legitimate contacts. For those on the Pro Plan, forms can be customized using CSS and JavaScript and seamlessly embedded into your website. Another key feature is abandoned submission tracking, which lets you follow up with users who start but don't complete the consent process. This feature is critical for maintaining comprehensive consent records.
Once consent is collected, keeping detailed records is the next step in ensuring ongoing compliance.
Document and Store Consent Records
Just as vendor audits safeguard data integrity, maintaining detailed consent records is essential for compliance. Reform automatically logs precise timestamps for when consent is given, along with the user’s specific identity - whether it's their name, email address, or session ID. The platform also stores a complete record of the form version shown to the user, including all the details about data-sharing practices disclosed at the time. This "master copy" serves as proof of exactly what the user agreed to.
Reform integrates smoothly with CRM and marketing automation tools, enabling real-time syncing of consent records with systems like HubSpot, Salesforce (Pro Plan), Zapier, and custom APIs. These integrations ensure that vendor management records are automatically updated whenever consent changes. This centralized system simplifies audit preparation - whether responding to regulatory requests for consent proof or meeting consumer data requests (which must be fulfilled within 45 days under the CCPA). With all records in one place, you can quickly provide the necessary documentation, ensuring compliance while strengthening data protection across your vendor relationships.
Conclusion
Achieving compliance with vendor data sharing under GDPR and CCPA demands a layered strategy. This involves conducting detailed due diligence, implementing strong security protocols, crafting clear contract terms, and managing consent effectively. It's crucial for organizations to understand that they remain responsible for personal data, even when third-party vendors are involved in processing it. This makes ongoing oversight of vendor relationships essential from beginning to end.
The financial consequences of non-compliance are steep. GDPR violations can result in fines reaching up to 4% of global annual revenue or €20 million, whichever is greater. Similarly, under the CCPA, intentional violations carry fines of $7,500 per incident, while non-intentional violations cost $2,500 each. On top of that, the CCPA allows consumers to claim damages of up to $750 per individual in cases of data breaches caused by insufficient security measures.
Technical safeguards are a key part of risk mitigation. Using tools like encryption and pseudonymization not only helps secure personal data but may also exempt organizations from certain breach notification requirements if the data remains unreadable to unauthorized parties. These safeguards should be paired with transparent data practices, ensuring users are informed about what personal information is collected and why it’s being shared with vendors.
Consent management tools, such as Reform, simplify compliance by automating the capture, storage, and documentation of user consents. When integrated into a broader vendor management strategy - which includes regular audits, well-defined data processing agreements, and zero-trust security models - these tools ensure the thorough documentation required by both GDPR and CCPA. By combining vendor vetting, contractual safeguards, robust security measures, and well-documented consent, organizations can establish a strong compliance framework that protects both their operations and the individuals whose data they handle.
FAQs
How do I know if a vendor is a processor or a joint controller?
To figure out whether a vendor is a processor or a joint controller, take a close look at your data processing agreements. A vendor qualifies as a processor if they handle data strictly according to your instructions. On the other hand, they are a joint controller if they have shared authority in deciding how the data is processed. Distinguishing between these roles is a key step in ensuring compliance with GDPR and other data protection regulations.
What should I include in a DPA to avoid CCPA “sale” or “sharing” issues?
To address potential CCPA "sale" or "sharing" concerns in a Data Processing Agreement (DPA), it's essential to include specific provisions. These should:
- Clearly state that the vendor is prohibited from selling or sharing personal information without explicit consumer opt-in.
- Require the vendor to implement mechanisms that honor consumer opt-out requests effectively.
- Mandate the maintenance of proper compliance documentation to align with CCPA requirements.
By including these measures, you can better ensure adherence to CCPA regulations while safeguarding consumer privacy.
How can I prove and audit user consent for vendor data sharing using Reform?
Organizations looking to ensure compliance with data privacy regulations like GDPR and CCPA can take proactive steps by maintaining detailed records of user consent. This includes keeping track of timestamps, the specific data shared, and user preferences. Reform's tools, such as real-time analytics and customizable forms, make it easier to monitor and document consent interactions. These features help create clear and reliable audit trails, simplifying the process of proving compliance when needed.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)