Best Practices for Data Transfer Impact Assessments

Transferring personal data internationally? You need a Transfer Impact Assessment (TIA).
A TIA evaluates whether data transfers to non-EEA countries meet GDPR standards, especially following the 2020 Schrems II ruling. This decision invalidated the EU-U.S. Privacy Shield, requiring businesses to assess risks like government surveillance in destination countries.
Key steps for effective TIAs:
- Map your data transfers: Identify exporters, importers, data types, and transfer methods.
- Analyze destination country laws: Assess government access risks and legal protections.
- Add safeguards: Use encryption, pseudonymization, or enhanced contractual clauses.
- Document everything: Keep detailed records to prove compliance during audits.
- Review regularly: Update assessments when laws or data processes change.
Tools like encryption and conditional routing can reduce risks and simplify compliance. Without proper TIAs, businesses risk fines of up to 4% of global turnover.
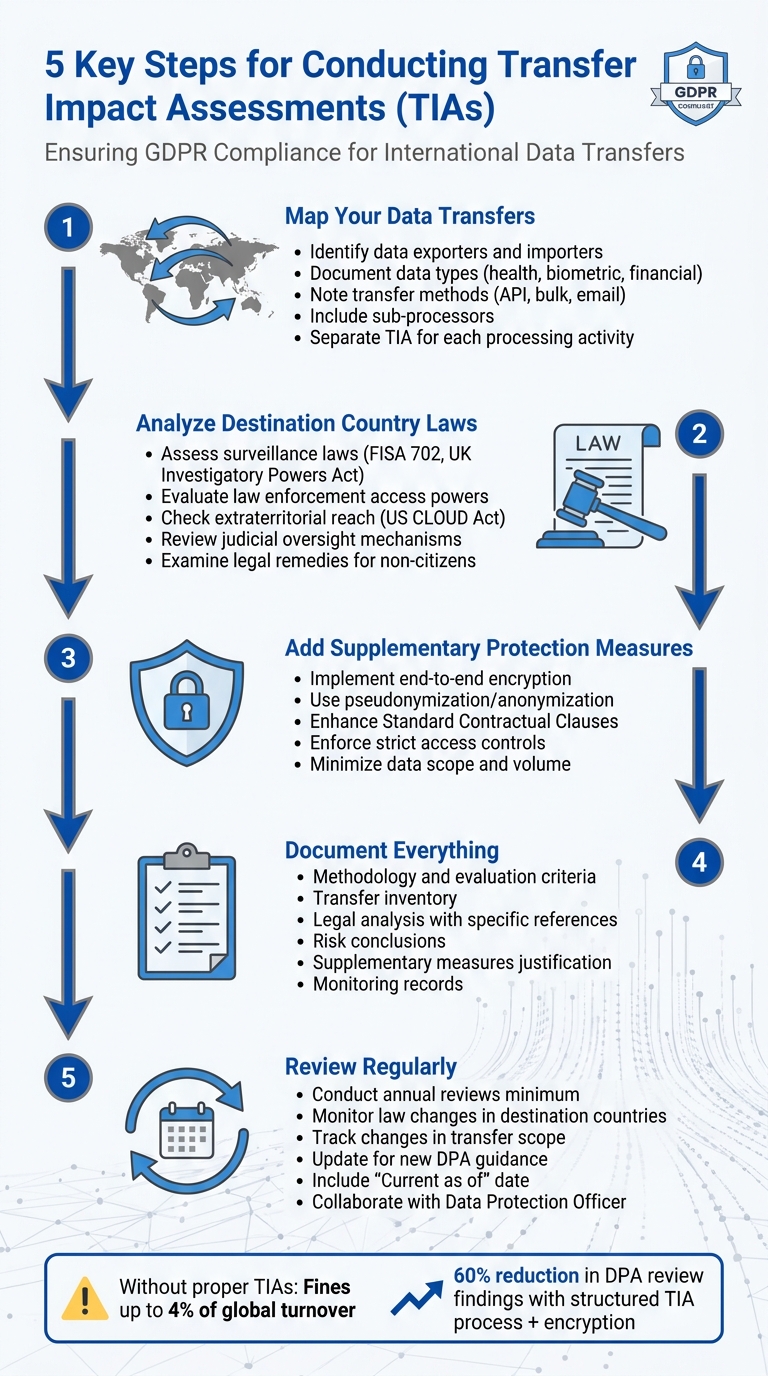
5 Key Steps for Conducting Transfer Impact Assessments (TIAs) Under GDPR
How to Conduct Effective TIAs
Map Your International Data Transfers
The first step in conducting a Transfer Impact Assessment (TIA) is to document every pathway where personal data crosses borders. This means identifying both obvious transfers, like those involving cloud storage, and less apparent ones, such as overseas technical support, analytics processing, or international backups.
Your mapping should include key details: the data exporter (your organization), the data importer (the recipient), any sub-processors involved in onward transfers, the types of data being transferred (e.g., health, biometric, financial, or children's data), how the data is transferred (API-to-API, bulk exchange, or email extraction), and whether the transfers are systematic or occur on an ad hoc basis. Avoid generalizing - conduct separate TIAs for each specific processing activity rather than relying on a single, organization-wide document. A thorough map provides the foundation for a detailed review of the destination country's data protection practices.
Assess Laws and Practices in Destination Countries
After mapping your transfers, the next step is to evaluate whether the destination country’s laws allow government access that exceeds EU-acceptable limits. Focus on key areas like surveillance laws (e.g., US FISA 702 or the UK Investigatory Powers Act), law enforcement access powers, and provisions with extraterritorial reach, such as the US CLOUD Act.
Go beyond theoretical legal frameworks by assessing the practical likelihood of government access. Consider the importer's profile - tech companies and government contractors often attract more scrutiny - the sensitivity of the data being transferred, and any historical patterns of government enforcement. Additionally, check whether the destination country offers independent judicial review of data requests and provides effective legal remedies for non-citizens whose rights may be affected. When documenting your TIA, rely on specific legal references and authoritative government resources rather than assumptions. Once this analysis is complete, you can focus on implementing measures to mitigate any identified risks.
Add Supplementary Protection Measures
With the legal landscape assessed, it's time to address potential risks by implementing supplementary protection measures. One of the most effective strategies is end-to-end encryption, ensuring that only you retain control of the encryption keys. This prevents the importer or local authorities from accessing the data in its original form.
Other technical measures include pseudonymizing or anonymizing the data before transfer. Contractual safeguards can also be strengthened by enhancing Standard Contractual Clauses with specific requirements, such as obligating the importer to notify you of government access requests when legally allowed. On an organizational level, enforce strict internal access controls and minimize the scope and volume of data being processed. Finally, work closely with data importers to understand local laws and infrastructure. While the ultimate responsibility for the TIA lies with the exporter, collaboration with the importer can provide valuable insights.
sbb-itb-5f36581
How to run a data transfer impact assessment after the Schrems II case
Document and Review Your TIAs
After implementing supplementary measures, it's essential to thoroughly document and regularly review your Transfer Impact Assessments (TIAs) to ensure they remain compliant over time.
Create Complete TIA Documentation
Proper TIA documentation serves as your evidence of compliance during reviews by Data Protection Authorities (DPAs). Without it, organizations risk being labeled non-compliant, which can lead to suspended data transfers and financial penalties.
Your documentation should address six key areas:
- Methodology: Detail the systematic approach you used, including evaluation criteria.
- Transfer Inventory: List data categories, processing purposes, recipient entities, and storage locations.
- Legal Analysis: Include specific references to third-country laws, focusing on government surveillance powers and redress mechanisms available to data subjects.
- Risk Conclusions: Identify vulnerabilities and assess the likelihood of government access based on the data importer's profile.
- Supplementary Measures: Justify your chosen safeguards, such as encryption or contractual protections.
- Monitoring Records: Maintain logs of safeguard performance, vendor audits, and any government access requests.
| Documentation Category | Key Elements to Include |
|---|---|
| Methodology | Systematic approach, risk evaluation criteria, and consulted sources. |
| Transfer Inventory | Data categories, processing purposes, recipient entities, and storage locations. |
| Legal Analysis | Specific references to third-country laws and surveillance powers. |
| Risk Conclusions | Vulnerabilities and likelihood of government access. |
| Supplementary Measures | Justification for technical, contractual, and organizational safeguards. |
| Monitoring Records | Logs of safeguard performance, audits, and government access requests. |
Avoid vague or general statements - DPAs frequently flag "superficial law analysis" as a major issue. Use reliable sources like government databases instead of media reports to strengthen your legal analysis. Including technical evidence such as system architecture diagrams, key management procedures, and audit logs can further substantiate your safeguards. DPAs are increasingly prioritizing technical evidence over contractual measures alone.
Interestingly, organizations that adopt a structured TIA process alongside customer-managed encryption report a 60% reduction in findings during DPA reviews. Once your documentation is complete, make it part of a routine review process to stay ahead of regulatory or operational changes.
Set Up Ongoing Monitoring and Updates
"A TIA is not a one-time exercise; it should be seen as an ongoing process to check for changes related to the data processing activities, to the nature of the data being processed, and to the changes in the legislation of the countries of import."
– Tudor Galos, Senior Privacy & AI Consultant at Tudor Galos Consulting
Periodic reviews - at least annually - are essential to account for changes in processing activities or laws. Establish clear reassessment triggers, such as updates to destination country surveillance laws, changes in your transfer scope (e.g., new vendors or data categories), or new DPA guidance. Always include a "Current as of" date on your TIA documentation to show that it’s actively maintained.
Collaborate with your Data Protection Officer to keep your documentation audit-ready. To simplify the process, consider using automation tools for tasks like data mapping, which can reduce the burden of manual tracking.
Using Digital Form Tools to Support TIAs
While TIAs focus heavily on meeting legal requirements, digital form tools can play a proactive role in reducing risks tied to data transfers. Platforms like Reform, which operate on no-code principles, offer practical ways to limit cross-border data flows and maintain tighter control over where personal data is processed. By combining thorough legal evaluations with advanced digital tools, organizations can address risks more effectively. These tools also complement the detailed TIA documentation and monitoring processes already discussed.
How Reform Supports Compliant Data Collection
One standout feature of Reform is its ability to enhance TIA compliance through conditional routing. This functionality lets you set up logic that automatically directs data based on where the respondent is located. For instance, if someone in Germany fills out a form, their data can be routed to a CRM hosted within the EU or assigned to a local team - ensuring the data stays within the respondent's jurisdiction.
Encryption adds another layer of protection, surpassing what contractual safeguards alone can provide. GDPR compliance expert Marc ten Eikelder emphasizes:
"Technical measures provide the strongest protection against government access - contractual measures alone are insufficient".
By controlling your own encryption keys, you can ensure that data remains inaccessible to third parties or government agencies in destination countries. This is especially critical when managing risks under laws like FISA 702 in the US.
Reduce Cross-Border Transfers Through Integrations
In addition to compliant data collection, direct integrations help secure data flows even further. Reform’s integrations with tools like HubSpot and Zapier eliminate the need for intermediary transfers through servers in third countries. By connecting Reform to a localized CRM instance, data can move directly from the form to your regional database, bypassing processors that might be subject to foreign surveillance laws.
For example, using Zapier to automate lead assignment ensures that data from EU respondents stays on EU servers, while data from US-based leads is processed domestically. This automated routing not only protects data integrity but also creates a clear audit trail for TIA documentation. Considering that EU Data Protection Authorities issued 127 corrective actions related to international data transfers between 2023 and 2024 - with inadequate TIAs as the main issue - a technical setup that limits cross-border transfers can significantly lower compliance risks.
Conclusion
Establishing a thorough TIA process is essential for ensuring compliance. Start by identifying every data category, its processing purpose, the entities involved, and where the data is stored. This approach helps address potential compliance gaps and lays the groundwork for confidently assessing risks.
When evaluating risks, consider both the legal framework and how it has been enforced historically, along with the data importer's reputation. To bolster security, implement strong encryption measures to protect data access.
Keeping accurate documentation and monitoring continuously can transform your TIA process from a mere formality into a dynamic compliance tool. Without up-to-date records, organizations risk being presumed non-compliant, which could result in suspended transfers or financial penalties. Automating reassessments based on changes in transfer scope or destination laws can further streamline this process.
Digital tools like Reform can help reduce the need for risky cross-border transfers. Features such as conditional routing and direct CRM integrations work alongside encryption to provide technical safeguards that go beyond contractual measures. When paired with comprehensive TIA documentation, these controls create a layered defense strategy that significantly reduces compliance risks. Together, these measures highlight the ongoing, evolving nature of TIA compliance.
As your business grows, laws shift, and risks develop, TIAs demand continuous attention. By combining detailed legal analysis, strong technical protections, and proper documentation, you can ensure compliant international data transfers while minimizing regulatory challenges.
FAQs
When do I need a TIA under GDPR?
A Transfer Impact Assessment (TIA) is required under GDPR when personal data is being transferred to a third country. Its purpose is to evaluate potential risks and ensure that the transfer aligns with GDPR principles. This is especially important given the ever-changing legal landscapes and updated guidance from supervisory authorities.
By conducting a TIA, organizations can better protect personal data and stay compliant with privacy regulations, ensuring that individuals' rights remain safeguarded throughout the process.
What makes a TIA “good enough” for a DPA audit?
A Transfer Impact Assessment (TIA) meets the mark for a Data Protection Authority (DPA) audit when it provides a comprehensive evaluation of both legal and practical risks tied to data transfers. It must demonstrate compliance with GDPR requirements and highlight any potential threats to data security and individuals' rights. Additionally, it should detail safeguards - such as encryption or contractual measures - especially when tackling challenges like third-country laws or government surveillance concerns.
Which safeguards reduce third-country access risk the most?
To mitigate the risk of unauthorized access from third countries, organizations can implement several critical measures:
- Data encryption: Use strong encryption standards like AES-256 or TLS 1.3 to protect sensitive information.
- Pseudonymization and minimization: Limit data exposure by anonymizing personal information and collecting only what's necessary.
- Access controls: Enforce multi-factor authentication and role-based permissions to ensure that only authorized individuals can access specific data.
- Secure transfer protocols: Rely on secure methods such as TLS 1.3, SFTP, or VPNs to safely transmit data.
Additionally, conducting regular risk assessments and monitoring helps identify and address vulnerabilities, ensuring ongoing protection.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)








