Cross-Border Data Transfers: Vendor Risk Checklist

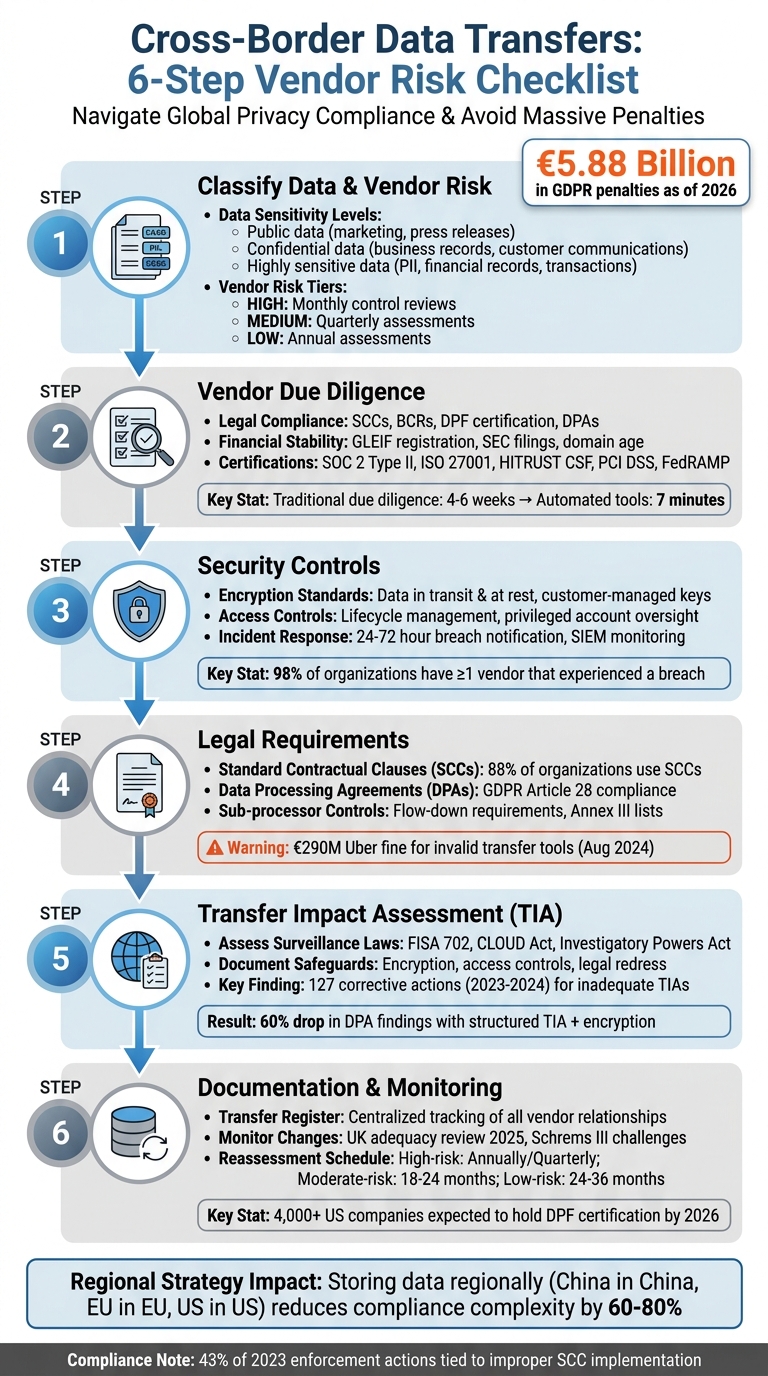
Cross-border data transfers are a minefield of global privacy rules. Mistakes can lead to massive fines - over $5.88 billion in GDPR penalties as of 2026 - and jeopardize crucial business deals. The Schrems II ruling also demands that organizations prove destination countries provide EU-equivalent data protection. Without proper safeguards, your data transfers could be illegal.
Here’s how to manage vendor risks effectively:
- Classify Data Sensitivity: Separate public, confidential, and highly sensitive data to prioritize resources.
- Vendor Risk Tiers: Categorize vendors by their data handling practices and the privacy laws in their operating countries.
- Due Diligence: Check legal compliance (e.g., SCCs, DPAs), operational stability, and certifications (e.g., SOC 2, ISO 27001).
- Security Measures: Ensure encryption, access controls, and incident response plans are robust.
- Legal Frameworks: Use Standard Contractual Clauses (SCCs) and Transfer Impact Assessments (TIAs) to meet GDPR standards.
- Ongoing Monitoring: Maintain a transfer register and reassess vendors regularly to stay compliant with evolving laws.
This checklist ensures your vendor management program is structured, compliant, and ready to handle global privacy challenges.
6-Step Cross-Border Data Transfer Vendor Risk Management Checklist
Cross-Border Data Transfer Regulations and Compliance Requirements | Exclusive Lesson
sbb-itb-5f36581
Step 1: Classify Data Types and Vendor Risk Levels
The first step is to pinpoint the types of data being transferred and identify who handles it. This process helps determine the level of scrutiny each vendor needs, ensuring resources are directed toward higher-risk transfers.
Identify Data Sensitivity Levels
Begin by listing all data processed by vendors and grouping it based on its sensitivity. According to the ICO's updated guidance (effective January 15, 2026), this process is now referred to as a "data protection test" under the Data (Use and Access) Act. This legal requirement outlines how to evaluate the protections in destination countries.
When classifying, it's essential to separate general personal data from data processed for law enforcement purposes under Part 3 of the Data Protection Act 2018. The latter demands a specialized assessment framework. For most commercial transfers, focus on three sensitivity categories:
- Public data: Includes marketing materials and press releases.
- Confidential data: Covers internal business records and customer communications.
- Highly sensitive data: Encompasses personally identifiable information (PII), financial records, and transaction details.
"Scope mistakes are expensive because they cascade into incorrect control design, wrong evidence requests, and missed dependencies during fieldwork." - Sebastien Ruosch, Executive Audit Director, Auditsuisse
Categorize Vendors by Risk Tier
After classifying your data, the next step is to assign vendors to appropriate risk tiers. This categorization depends on what data they handle, where they operate, and how they secure it. Vendors managing encryption keys or handling PII in countries with weak privacy laws represent the highest risk. Medium-risk vendors typically operate in countries requiring Standard Contractual Clauses (SCCs), while low-risk vendors are those with limited data access within the EEA or your local jurisdiction.
To accurately assess vendor risk, examine their certifications (e.g., ISO 27001, SOC 2), access control measures, and data retention policies. This risk tiering determines the level of oversight needed:
- High-risk vendors: Require monthly control reviews and continuous monitoring.
- Low-risk vendors: May only need annual assessments.
Maintain a detailed data inventory that tracks what each vendor processes, where the data is stored, and how it moves across borders. This ensures your risk classifications remain accurate and up to date.
This foundational classification sets the stage for performing due diligence in the next steps.
Step 2: Vendor Due Diligence Checklist
Once you've classified your data, the next step is conducting thorough due diligence to assess vendor compliance, stability, and security measures. After categorizing vendors based on risk, it's time to dig deeper into their ability to safeguard your data. This involves reviewing their documentation and operational reliability.
Evaluate Regulatory Compliance
Start by confirming the vendor's legal data transfer mechanisms. These could include Adequacy Decisions, Standard Contractual Clauses (SCCs), Binding Corporate Rules (BCRs), or the EU-US Data Privacy Framework (DPF). If SCCs are in use, ensure they follow the updated 2021 modules:
- Module 1: Controller-to-Controller
- Module 2: Controller-to-Processor
- Module 3: Processor-to-Processor
- Module 4: Processor-to-Controller
For U.S.-based vendors, check their DPF certification directly on the Department of Commerce website. Privacy experts often recommend using SCCs as a backup, even for DPF-certified vendors, given ongoing legal challenges like Schrems III.
Examine the vendor's Data Processing Agreement (DPA) to ensure it meets Article 28 requirements. This includes specifying technical and organizational measures (TOMs) and covering all sub-processor transfers under valid mechanisms. Pay attention to sub-processor lists and ensure the DPA accounts for any changes to these arrangements.
| Destination Country | Key TIA Issues | Compliance Status (as of 2026) |
|---|---|---|
| United States | FISA Section 702 surveillance | DPF adequacy for certified entities; SCCs + TIA for others |
| China | PIPL data access; national security laws | Requires CAC security assessment or standard contracts |
| India | Interception powers under IT Act | DPDP Act rules apply; surveillance framework is a TIA risk |
| Canada | PIPEDA limitations | Partial adequacy (commercial organizations only) |
| United Kingdom | Post-Brexit alignment | Adequacy decision in place (subject to periodic review) |
Once you've confirmed legal and contractual compliance, shift your focus to the vendor's operational stability.
Assess Financial and Operational Stability
The vendor's long-term reliability is essential for protecting your data. Verify their status as a registered legal entity through the Global Legal Entity Identifier (GLEIF) database. For publicly traded companies, check their SEC EDGAR filings for 10-K disclosures, litigation risks, or enforcement actions that might indicate instability.
Document the vendor's country of incorporation and any parent or subsidiary relationships, as these can influence regulatory exposure and the likelihood of data disclosure under foreign laws. Additionally, review WHOIS records to determine domain age - an older domain (e.g., 30 years) often signals a more stable operation.
Request the vendor's Business Continuity and Disaster Recovery (BCDR) plans, which should outline Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO) by jurisdiction. Confirm their cyber liability insurance covers breach-related risks. Also, ask for a Data Flow Diagram to map out subprocessors' locations and cloud regions.
"Your security program is only as strong as your weakest vendor." - CISOSHARE
Review Certifications and Audits
Certifications provide valuable insight into a vendor's adherence to recognized security standards. Request a SOC 2 Type II report, which evaluates control effectiveness over a 6–12 month period, offering more depth than a Type I review. These reports aren’t publicly available, so you’ll need to request them directly from the vendor.
Look for ISO 27001 certification, which confirms the vendor has an established Information Security Management System (ISMS). For vendors managing Protected Health Information (PHI), verify their HITRUST CSF certification. If the vendor handles payment card data, request their PCI DSS Attestation of Compliance (AoC). For those working with U.S. government data, confirm FedRAMP authorization through the official FedRAMP Marketplace (marketplace.fedramp.gov) rather than relying on vendor claims.
Traditional due diligence processes, which often rely on manual questionnaires, can take 4–6 weeks. However, as of 2026, automated tools can now analyze sanctions, cyber risks, and adverse media in just 7 minutes. While a vendor's "Trust Center" may list certifications, treat these as self-reported until you’ve reviewed the actual audit reports or certificates.
"GDPR compliance readiness has shifted from a procurement checkbox to a core trust signal in enterprise buying cycles." - Sebastien Ruosch, Executive Audit Director, Auditsuisse
Ensure your contract includes provisions for at least one annual audit - remote or on-site - or requires third-party reports that are no older than 12 months. A vendor's refusal to sign a compliant DPA is a serious warning sign, indicating potential gaps in their privacy and security practices.
Step 3: Security Controls and Technical Safeguards
Once you've confirmed a vendor's compliance and stability, the next step is to dig into their technical security measures. Encryption and access controls are your first line of defense when transferring data across borders, especially to regions with extensive surveillance laws. Make sure these measures are clearly outlined in your vendor contracts under the Technical and Organizational Measures (TOMs) annex, as required by Standard Contractual Clauses.
Encryption Standards and Access Controls
Start by verifying that your vendor uses strong encryption for both data in transit and at rest. For transfers involving high-risk data, consider adding pseudonymization to make it harder to link the data back to specific individuals.
Another key point: check if your vendor offers customer-managed encryption. This setup allows you to maintain exclusive control over the encryption keys within your jurisdiction. Why does this matter? Even if the vendor is served with a government access request, the data will remain unreadable without your keys. German Data Protection Authorities have emphasized that encryption controlled by the data exporter is one of the most effective safeguards for ensuring adequacy.
Next, take a close look at the vendor's access lifecycle management. This should cover onboarding new users, managing permissions, handling role changes, and offboarding. Pay special attention to how they manage privileged accounts, as these have elevated access and require strict oversight to prevent unauthorized use. Ask for evidence of periodic access certifications, where the vendor reviews and adjusts permissions to match each user's current responsibilities.
"Mature programs build control operations into engineering, IT, and business processes instead of running them as separate compliance workstreams."
- Sebastien Ruosch, US & Swiss Licensed CPA
You should also confirm that any sub-processors used by the vendor maintain equivalent encryption and security measures for "onward transfers". For instance, if your SaaS vendor in the U.S. relies on AWS for cloud hosting, ensure AWS meets the same encryption standards. To keep things on track, schedule monthly reviews with your engineering and security teams to check for "control drift" and confirm that encryption protocols remain effective.
With encryption and access controls squared away, the focus shifts to ensuring quick detection and response in case of a security incident.
Incident Response and Monitoring
Preventive measures like encryption and access controls are essential, but you also need a solid plan for handling incidents. Ask your vendor for a copy of their Incident Response (IR) plan. This should outline key roles (like an incident commander), escalation procedures, and specific steps for dealing with cross-border data issues. To ensure the plan is more than just theory, request evidence of recent testing, such as a tabletop exercise or functional drill.
Your contract should also define clear breach notification timelines. For vendors handling your most sensitive data, aim for a 24-hour notification window, with a broader range of 24 to 72 hours for other cases. Be sure to explicitly define what counts as a "breach" to avoid confusion during a crisis.
Continuous monitoring is another must-have. Ensure the vendor uses tools like centralized logging, 24/7 critical event alerting, and a Security Information and Event Management (SIEM) system. Audit logs should track any decryption requests under customer-managed encryption, giving you a clear record of who accessed your data and when.
For added peace of mind, consider external monitoring tools like BitSight or SecurityScorecard. These platforms can provide independent security ratings and alert you to potential third-party compromises. This is especially important when you consider that 98% of organizations have at least one vendor that has experienced a breach, and 62% of breaches involve third-party vectors.
Finally, make sure your contract includes audit rights. These allow you to inspect the vendor's security logs and incident response records after a suspected breach. Vendors should also notify you of incidents involving their sub-processors, as these can often be weak links. Under Standard Contractual Clauses, vendors are required to inform you of legally binding requests for data access from public authorities, unless prohibited by law.
| Essential IR Contract Clause | Purpose |
|---|---|
| Incident Notification | Specifies timeframe (24–72 hours) and required details for breach reports |
| Cooperation Duties | Requires vendor assistance with investigations and regulatory filings |
| Audit Rights | Allows inspection of vendor systems and records post-incident |
| Data Return/Deletion | Ensures secure data return or deletion if the relationship ends after a breach |
Step 4: Contractual and Legal Requirements
Once your technical safeguards are in place, it's time to focus on the legal framework for handling data across borders. Contracts aren't just formalities - they turn commitments into enforceable obligations and serve as your safety net when things go sideways. According to data, 88% of organizations rely on Standard Contractual Clauses (SCCs) for international data transfers, making them the industry standard.
Incorporate Standard Contractual Clauses (SCCs)
SCCs complement your technical measures by adding a legal layer of protection for data transfers. These clauses are pre-approved templates from the European Commission that allow personal data to be legally transferred outside the EU. For vendor relationships, Module 2 (Controller-to-Processor) is typically the right choice, ensuring data is processed strictly under your instructions.
It's critical to note: you can't change the core text of the SCCs. You can select the applicable module, fill in the necessary details, and add extra safeguards to strengthen protection. However, altering the standard language could invalidate the agreement and require prior approval from a data protection authority. For example, in August 2024, the Dutch Data Protection Authority fined Uber €290 million for transferring European taxi driver data to the U.S. without valid transfer tools. Uber had stopped using SCCs after earlier frameworks expired, leading to non-compliance.
Additionally, you must conduct a Transfer Impact Assessment (TIA) under Clause 14 to confirm that the destination country's laws don't undermine SCC protections. Ensure vendors notify you of any binding government data access requests under Clause 15. Regulators take these requirements seriously - 43% of enforcement actions in 2023 were tied to improper SCC implementation.
Don't forget the annexes:
- Annex I: Details on parties and data being transferred.
- Annex II: Technical and organizational measures.
- Annex III: Sub-processor lists.
These annexes provide evidence of your compliance efforts, demonstrating accountability to regulators.
Address Data Processing Agreements (DPAs)
Under GDPR Article 28, a Data Processing Agreement (DPA) is mandatory when you hire a vendor to process personal data. While SCCs handle cross-border transfers, the DPA outlines the vendor's broader responsibilities. The 2021 SCCs integrate Article 28, so a single agreement can often cover both SCC and DPA requirements.
Your DPA should clearly define roles: you're the Data Controller (deciding how and why data is processed), and the vendor is the Data Processor (acting only on your documented instructions). This distinction is crucial because if the vendor uses your data for purposes like advertising or product development, they could be reclassified as a Joint Controller, altering liability under GDPR Articles 26 and 82.
The agreement must include eight key elements from GDPR Article 28:
- Subject matter and duration.
- Documented instructions.
- Confidentiality requirements.
- Security measures.
- Sub-processor rules.
- Assistance with data subject rights.
- Breach notification timelines.
- Data return or deletion after termination.
For breach notifications, vendors typically need to inform you within 72 hours of discovering an incident. For data deletion, the standard is often 30 days after contract termination.
"A vendor's refusal to sign a compliant DPA is a major red flag. If they push back or offer a weak alternative, you should seriously reconsider working with them."
- Calvin Choong, Product Strategy Lead, Vendorfi
Also, negotiate audit rights upfront. If vendors resist direct audits, require them to provide third-party certifications like SOC 2 Type II or ISO 27001 within 30 days of issuance. These reports offer independent verification of their security practices without requiring on-site inspections.
Define Onward Transfer Restrictions
Your vendor isn't working in isolation - they likely use sub-processors like cloud providers, payment services, or analytics platforms. To maintain control, extend your contractual safeguards to these third parties.
Under Clause 8.7 of the SCCs, your vendor can't share data with third parties outside the EU unless those parties agree to the same SCCs, are in a country with an adequacy decision, or meet equivalent safeguards.
Decide whether the vendor has "general" or "specific" authorization to engage sub-processors:
- General authorization: The vendor can add sub-processors but must notify you in advance (e.g., 30, 60, or 90 days) and allow you to object within a set timeframe (e.g., 14 to 30 days).
- Specific authorization: You must approve each sub-processor individually before engagement.
Regardless of the approach, ensure the vendor signs agreements with sub-processors that impose the same data protection obligations outlined in your original DPA. This "flow-down" requirement holds the vendor accountable for any sub-processor breaches.
Keep an updated Annex III listing all authorized sub-processors, their locations, and their roles. Consider using the optional "docking clause" (Clause 7) from the 2021 SCCs to simplify adding new parties, such as additional sub-processors or affiliates, without renegotiating the entire agreement. This can reduce administrative headaches as your vendor's operations evolve.
Step 5: Conduct a Transfer Impact Assessment (TIA)
After implementing contractual and technical safeguards, a Transfer Impact Assessment (TIA) ensures that the legal environment in the destination country aligns with EU data protection standards. Even with Standard Contractual Clauses (SCCs) and Data Processing Agreements (DPAs), a properly documented TIA is crucial to validate your legal protections. Without this documentation, SCCs may not provide sufficient protection. From 2023 to 2024, EU Data Protection Authorities issued 127 corrective actions related to international data transfers, with inadequate TIAs being the most common issue. Regulators require a systematic and well-documented evaluation to confirm that the legal framework in the destination country does not undermine these safeguards.
Assess Surveillance Laws and Government Access
Part of your TIA involves identifying and analyzing the surveillance laws and government data access policies in the destination country. For example, in the U.S., this includes examining Section 702 of the Foreign Intelligence Surveillance Act (FISA) and the CLOUD Act. In the UK, the Investigatory Powers Act is a key law to review. Use reliable sources, such as government websites and legal databases, rather than general media reports for this analysis.
Your assessment should explore critical questions, such as:
- Can authorities compel your vendor to disclose personal data?
- Are bulk data collection or indiscriminate surveillance practices allowed?
- Is there independent judicial oversight, or can intelligence agencies access data without court approval?
Compare the findings to EU standards, which require that government access be limited to what is necessary and proportionate in a democratic society. This step builds on earlier due diligence by focusing on the legal risks posed by government access to data.
In addition to legal texts, consider practical risk factors. For instance, is your vendor a telecommunications provider or a government contractor? Are you transferring highly sensitive data, such as biometrics, location data, or financial records? Also, look at historical enforcement practices - some laws may exist but are rarely enforced. Interestingly, organizations that pair a structured TIA approach with customer-managed encryption have reported a 60% drop in findings during data protection authority (DPA) examinations.
Document Safeguards and Legal Redress Mechanisms
After identifying potential risks, document the safeguards in place to mitigate them. For instance, encryption measures can render data unreadable, even under broad surveillance laws. Ensure that encryption keys are generated and stored exclusively under your control within the EU.
"Technical measures provide the strongest protection against government access - contractual measures alone are insufficient." - Kiteworks
Another key step is to determine whether individuals can seek legal redress in the destination country. Can data subjects file lawsuits in local courts? Are there independent oversight bodies monitoring government surveillance activities?
For data transfers to the U.S., include an assessment of the protections introduced by Executive Order 14086, which supports the EU-U.S. Data Privacy Framework. Finally, plan to review your TIA at least once a year - or sooner if the destination country updates its surveillance or data access laws.
Step 6: Establish Documentation and Monitoring Protocols
After completing your Transfer Impact Assessment (TIA), it's time to set up systems for ongoing documentation and monitoring. These processes ensure your vendor risk management program stays current with regulatory changes. Without them, your program can quickly become outdated.
Maintain a Transfer Register
A transfer register acts as a centralized hub for tracking all vendor relationships and cross-border data flows. It consolidates critical vendor details, making it easier to adjust for compliance. Key information to include in this register:
- Vendor's legal entity name
- Risk tier
- Destination country
- Transfer mechanism (e.g., SCC module number, BCR, or EU‑U.S. Data Privacy Framework)
- Data subject categories
- Data types (e.g., personal, sensitive, financial, biometric)
- Most recent TIA date and findings
- Supplementary measures (e.g., encryption, access controls)
- Contract dates and notice periods
Some regulations, like the Digital Operational Resilience Act (DORA), now require formal documentation of third-party relationships, particularly for ICT providers in specific sectors. This register not only meets those requirements but also provides a comprehensive compliance snapshot when combined with earlier risk assessments.
Monitor Regulatory and Geopolitical Changes
Keep an eye on changes to laws, contractual clauses, and regulatory guidance. For instance, the UK adequacy decision adopted in June 2021 includes a sunset clause, meaning it will be reviewed in 2025. Similarly, if you're using the EU‑U.S. Data Privacy Framework, be aware of ongoing legal challenges, such as "Schrems III", which could impact its validity.
"TIAs are not one-time exercises - reassess when: destination country law changes, SCCs are amended, significant new guidance from EDPB or national DPAs emerges." - ECOSIRE Research and Development Team
For U.S. transfers, confirm your vendor's active certification on the official Data Privacy Framework website (dataprivacyframework.gov). Even if relying on adequacy decisions, keep backup documentation of SCCs to prepare for potential invalidation or suspension of those decisions. Stay updated on regional changes to outbound transfer rules and data localization requirements.
Schedule Regular Reassessments
Create a formal schedule for reassessing vendors based on their risk level:
- High-risk vendors: Review at least annually or quarterly if risks increase.
- Moderate-risk vendors: Reassess every 18 to 24 months.
- Low-risk vendors: Review every 24 to 36 months or before contract renewal.
Unscheduled reassessments may also be necessary. For example, if a vendor experiences a breach, changes sub-processors, merges with another company, or if a destination country's surveillance laws are updated. Automated tools like BitSight or SecurityScorecard can help you continuously monitor vendor security and compliance. Conduct monthly reviews with relevant teams to catch any compliance issues early.
When a vendor relationship ends, ensure your register includes a checklist for revoking access and obtaining data deletion certificates. This final step helps close the loop on compliance and security.
Conclusion
Managing cross-border data transfers effectively demands a well-structured and consistent approach to vendor risk management. The six-step checklist in this guide - covering everything from classifying data types and conducting due diligence to implementing security controls, establishing contractual protections, performing Transfer Impact Assessments (TIAs), and maintaining proper documentation - provides a clear framework to navigate global compliance challenges.
Regulations in this space are constantly changing. Currently, Standard Contractual Clauses (SCCs) are the backbone for more than 90% of cross-border data transfers. However, enforcement actions highlight the need to keep these mechanisms under regular review. For example, Meta faced a EUR 120 million fine in May 2023 for continuing to rely on the invalidated Privacy Shield framework, underscoring the financial risks of failing to adapt to regulatory updates.
A tailored regional data strategy can simplify compliance significantly:
"Regional data architecture - storing China-originated data in China, EU data in EU regions, and US data in US-certified facilities - reduces cross-border compliance complexity by 60-80% compared to centralized global storage strategies." - AgentScout Intel
To stay ahead, schedule quarterly reviews of transfer mechanism validity and monthly checks for US Data Privacy Framework (DPF) certifications. With around 4,000 US companies expected to hold DPF certification by 2026, it's essential to verify their status on dataprivacyframework.gov before initiating any data transfers to avoid compliance pitfalls. For outbound transfers from China, mandatory security assessments kick in when processing either 100 million personal data records or 100,000 sensitive records, with penalties reaching as high as CNY 5 million or 5% of global annual turnover.
Beyond technical and contractual safeguards, maintaining an agile risk management program is critical. This ensures your organization can respond swiftly to changes in the legal landscape. Automating compliance dashboards to track SCC expiration dates, filing statuses, and TIA progress in real time can enhance your ability to act decisively. Additionally, preserving the capability to suspend transfers immediately if destination country protections fail to meet EU standards ensures your compliance efforts remain both proactive and strategic. By taking these steps, compliance evolves from a routine task into a key strength for your organization.
FAQs
Do I always need SCCs for cross-border data transfers?
No, Standard Contractual Clauses (SCCs) aren’t always mandatory. They’re typically required when personal data is being transferred outside the EU/EEA to a country that doesn’t have an adequacy decision or another approved mechanism in place, such as Binding Corporate Rules (BCRs) or specific derogations. It’s crucial to ensure that your chosen data transfer method aligns with the relevant data protection laws.
What should a Transfer Impact Assessment (TIA) include?
A Transfer Impact Assessment (TIA) involves several important steps to ensure compliance with global data protection laws. These steps include:
- Mapping transfer details: Clearly identifying the data being transferred, the parties involved, and the purpose of the transfer.
- Identifying the transfer mechanism: Determining the legal basis or framework, such as Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs), that governs the transfer.
- Evaluating the destination country’s legal framework: Assessing the laws and practices of the recipient country to determine if they provide an adequate level of data protection.
- Assessing protections: Reviewing the technical and organizational measures in place to ensure they meet the required standards for safeguarding data during and after the transfer.
These steps are essential for maintaining compliance with regulations that oversee cross-border data transfers.
How often should I reassess high-risk vendors?
High-risk vendors need to be reviewed every year to confirm they’re still meeting data protection laws and to account for any shifts in their risk levels. These regular check-ins are crucial for keeping them accountable and reducing the risks tied to cross-border data transfers.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)








