EU Court Cases on Data Transfer Violations: Lessons

GDPR violations can cost businesses up to 4% of global revenue. Recent EU court rulings have made cross-border data transfers more challenging, with stricter requirements and higher penalties for non-compliance. Here's what you need to know:
-
Key Cases Reshaping Rules:
- Schrems II (2020): Invalidated the EU-US Privacy Shield, introduced Transfer Impact Assessments (TIAs), and fined Meta €1.2 billion for inadequate safeguards.
- General Court Ruling (2025): Upheld the EU-US Data Privacy Framework (DPF), simplifying transfers to certified U.S. companies but warned of future challenges.
- TikTok Fine (2025): €530 million fine for failing to protect EEA user data from Chinese access, setting a precedent for remote access violations.
-
Compliance Challenges:
- TIAs are mandatory for all data transfers outside the EEA.
- Businesses must assess foreign surveillance laws and implement safeguards like encryption.
- Over 47% of organizations struggle with these requirements.
-
Practical Solutions:
- Use customer-managed encryption and EU-based servers.
- Regularly update TIAs and monitor adequacy decisions like the DPF.
- Audit third-party tools to prevent accidental data transfers.
With enforcement ramping up and potential new challenges like "Schrems III", businesses must prioritize compliance to avoid fines and disruptions.
🚨 TikTok GDPR Violation: What Privacy Pros Need to Know About the DPC's Final Decision
sbb-itb-5f36581
Major EU Court Cases on Data Transfer

Major EU Data Transfer Court Cases and Penalties Timeline 2020-2025
Three major rulings have reshaped how businesses manage cross-border data transfers. These decisions highlight the weaknesses in current frameworks and drive essential changes in compliance practices.
Schrems II Judgment (2020)
In July 2020, the Court of Justice of the European Union (CJEU) struck down the EU-US Privacy Shield framework, which had been used by around 5,000 organizations. The court found that US surveillance laws, particularly FISA Section 702 and Executive Order 12333, did not meet EU standards for proportionality or judicial redress.
"The Privacy Shield framework is incompatible with the protections afforded and required by EU law." - Court of Justice of the European Union
Although Standard Contractual Clauses (SCCs) remained valid, the ruling introduced a new requirement: Transfer Impact Assessments (TIAs). These assessments require businesses to evaluate, on a case-by-case basis, whether the destination country's legal framework aligns with EU standards. If gaps are identified, companies must implement additional safeguards, such as end-to-end encryption with the service provider unable to access decryption keys.
The consequences of non-compliance have been severe. For example, Meta Ireland faced a €1.2 billion fine following this decision.
General Court Ruling on EU-US Data Privacy Framework (2025)
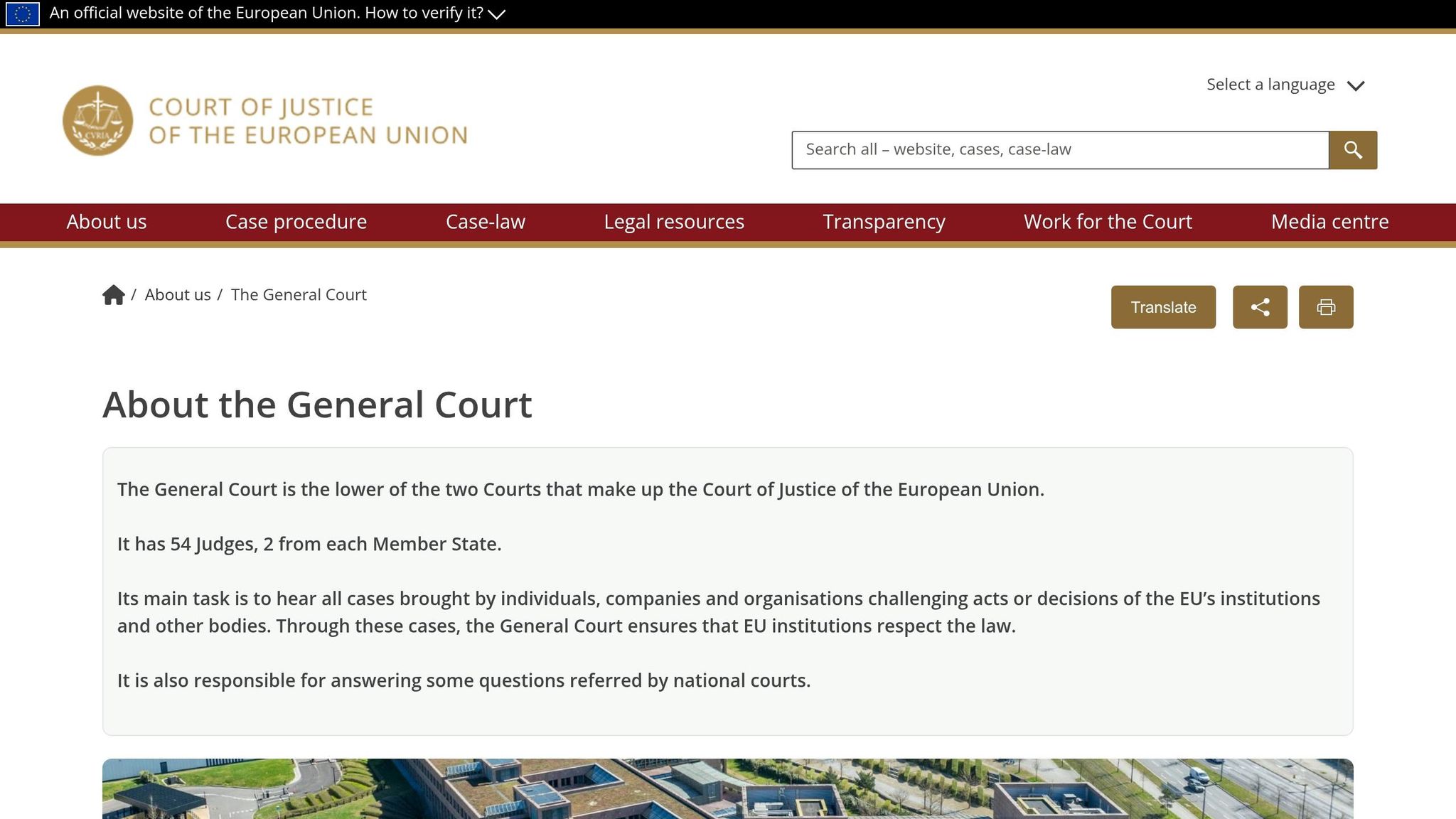
Building on the Schrems II decision, the General Court clarified the rules for transatlantic data transfers. On September 3, 2025, the court upheld the EU-US Data Privacy Framework (DPF) in the case Latombe v. Commission (T-553/23), providing some stability for businesses. The court highlighted improvements made under Executive Order 14086, including the establishment of the Data Protection Review Court (DPRC).
The DPRC, consisting of at least six judges appointed for renewable four-year terms, operates independently. Judges can only be removed for specific reasons like misconduct or neglect of duty. The court determined that this setup offers an "essentially equivalent" level of protection to EU judicial standards.
"The DPF is here to stay - at least for now. The General Court's endorsement provides a certain degree of legal certainty for organizations relying on the DPF for transatlantic data transfers." - Tom De Cordier, Partner, CMS
For businesses, this means transfers to DPF-certified US companies do not require the same additional safeguards as transfers to countries without adequacy decisions. Still, organizations should confirm their US partners' active certification and maintain SCCs as a fallback in case of further legal challenges.
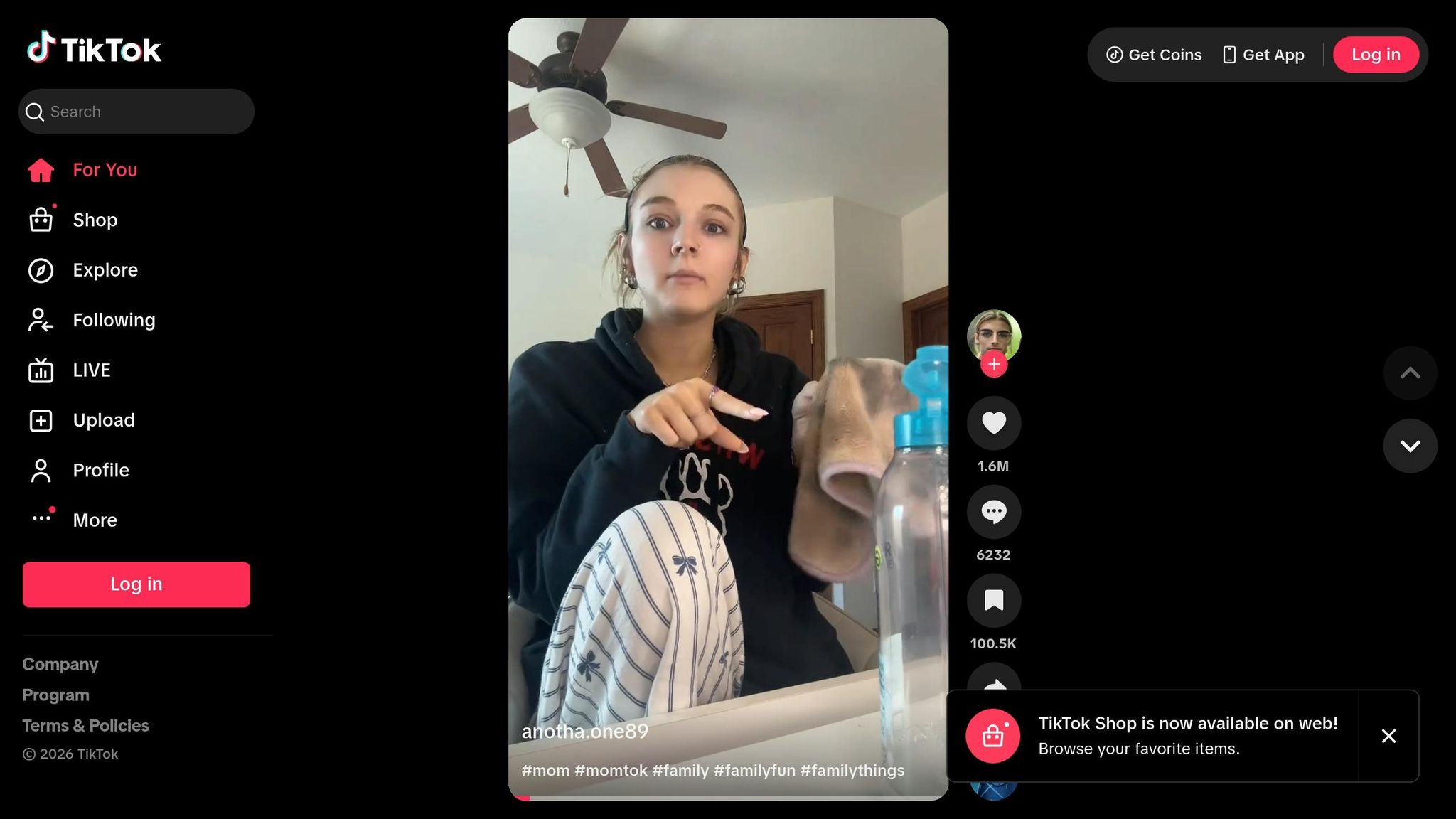
TikTok Remote Access Fine by Irish DPC (2025)
In May 2025, the Irish Data Protection Commission (DPC) fined TikTok Technology Limited €530 million. This included €485 million for failing to meet Article 46 (transfer safeguards) and €45 million for breaching Article 13(f) (transparency). The case set a precedent by confirming that remote access to data by staff in a third country counts as a data transfer, even if the data is physically stored elsewhere.
The DPC determined that TikTok's safeguards were insufficient to protect the data of 159 million EEA users from access by China-based staff under national security laws. Additionally, TikTok admitted in April 2025 that it had provided false information during the investigation, revealing that some EEA user data had been stored on servers in China.
"TikTok's personal data transfers to China infringed the GDPR because TikTok failed to verify, guarantee and demonstrate that the personal data of EEA users, remotely accessed by staff in China, was afforded a level of protection essentially equivalent to that guaranteed within the EU." - Graham Doyle, Deputy Commissioner, Irish Data Protection Commission
The DPC ordered TikTok to comply within six months or face a total suspension of data transfers to China. This case emphasizes that ongoing technical projects, like TikTok's "Project Clover", do not justify current non-compliance. Companies must ensure that data transfers meet EU standards, regardless of future plans. These rulings highlight the pressing need for strong data protection measures, which will be discussed further in the upcoming section on practical compliance lessons.
How Court Rulings Affect Business Operations
Recent EU court decisions have shifted the responsibility for managing data transfers outside the European Economic Area (EEA) from a simple legal requirement to an ongoing operational task. Businesses must now actively ensure compliance, going beyond just contractual assurances. Between 2023 and 2024, EU Data Protection Authorities issued 127 corrective actions related to international data transfers, with the most common violation being inadequate Transfer Impact Assessments (TIAs).
Failing to comply with these regulations can lead to hefty penalties - up to $21.6 million or 4% of global turnover. To address these challenges, many organizations are implementing stronger technical safeguards.
Supplementary Measures and Technical Safeguards
Following rulings like Schrems II, companies are required to go beyond contractual agreements and implement stronger technical protections. Standard Contractual Clauses alone no longer suffice. The European Data Protection Board has emphasized that technical measures are more reliable than contractual ones, as contracts cannot prevent government authorities from accessing data under local laws.
"Technical measures provide the strongest protection against government access - contractual measures alone are insufficient."
- Marc ten Eikelder, updated February 18, 2026
One of the most effective strategies is customer-managed encryption using EU-based Hardware Security Modules (HSMs). These tools allow businesses to generate and store encryption keys locally, ensuring that neither the service provider nor foreign governments can access the data. Organizations adopting this approach, combined with well-structured TIAs, have reported a 60% drop in findings from Data Protection Authority examinations.
Other technical safeguards include pseudonymization and data minimization. However, for these measures to be effective, encryption keys must remain inaccessible to third-country importers or government authorities.
| Measure Type | Effectiveness Against Government Access | Examples |
|---|---|---|
| Technical | High (if keys are held by the exporter) | Customer-managed encryption, pseudonymization |
| Contractual | Low (cannot override local law) | Transparency reports, notification obligations |
| Organizational | Medium (supports governance) | Data minimization policies, internal access audits |
Conducting Transfer Impact Assessments (TIAs)
In addition to technical safeguards, businesses must perform a thorough assessment for every data transfer. A TIA is required for all transfers using Standard Contractual Clauses and must be more than a superficial checklist. Regulators expect detailed documentation of the analysis.
Start by mapping all data flows, including often-overlooked ones like cloud backups, remote support, and analytics. Many organizations - nearly half - still struggle to fully comply with post-Schrems II requirements.
Your TIA should include a detailed evaluation of the destination country's laws. For example, consider legislation like FISA Section 702 in the US, the UK Investigatory Powers Act, or China's National Intelligence Law. Analyze whether these laws could compel access to your data and whether your technical safeguards can effectively block such access.
It’s also crucial to document your findings, methodologies, and any additional measures taken. Set up internal protocols to review and update TIAs regularly, especially when there are changes in the destination country’s laws or an increase in transfer volumes.
Monitoring Adequacy Decisions and Legal Updates
Adequacy decisions, which allow for simplified data transfers, are not permanent and can be overturned even after years of reliance . For example, the EU–US Data Privacy Framework, upheld in September 2025, has provided some stability for transfers to certified US companies. However, privacy advocates continue to challenge these mechanisms .
"The principle that transfer mechanisms can be invalidated - even ones that companies have relied on for years - is now established."
- Sarah Mitchell, GDPRScoreCheck
To prepare for potential disruptions, businesses should maintain fallback mechanisms. This includes keeping Standard Contractual Clauses and Transfer Impact Assessments ready as backup plans . By early 2026, over 3,000 US companies had self-certified under the Data Privacy Framework, but invalidating transatlantic frameworks could cost the digital trade sector between $20.5 billion and $33.5 billion.
Schedule regular reviews - annually or biennially - of your TIAs to ensure continued compliance. Keep an eye on oversight bodies like the US Privacy and Civil Liberties Oversight Board and the Data Protection Review Court to confirm that protections remain effective . Lastly, update vendor Data Processing Agreements to reference the modernized 2021 Standard Contractual Clauses instead of outdated versions.
Practical Lessons for Cross-Border Data Compliance
The recent rulings highlight the importance of turning legal mandates into practical, everyday safeguards for businesses handling cross-border data.
Conducting Realistic Risk Assessments
Compliance efforts today emphasize proportional safeguards based on real-world risks. The European Data Protection Board has clarified that businesses are required to provide "essentially equivalent" protection for transferred data, not absolute equivalence.
"A strict similarity or absolute equivalence between law is therefore not required, only an essential equivalence is deemed sufficient."
- General Court of the European Union
To meet this standard, focus your risk assessments on critical factors like the sensitivity of the data and the likelihood of exposure to foreign surveillance laws. Tailor technical safeguards to address the most significant risks instead of applying one-size-fits-all measures. For instance, companies that combined structured Transfer Impact Assessments with customer-managed encryption were better equipped to handle regulatory reviews and reduce compliance challenges.
A practical approach includes mapping out data flows by sensitivity level and applying encryption to high-risk transfers. This targeted strategy aligns with regulatory expectations while keeping compliance efforts cost-effective.
In addition to assessing risks, it’s crucial to choose the right tools to avoid accidental transfer violations.
Using Tools to Simplify Compliance
Data collection often becomes a weak link in compliance efforts. Many businesses unintentionally breach regulations by using third-party tools - like form builders, analytics platforms, or marketing services - that route data through servers outside the European Economic Area (EEA). A notable example occurred in January 2025 when the General Court ordered the European Commission to pay €400 in damages after an individual's IP address was unlawfully transferred to Meta in the US via a "Sign in with Facebook" button on an EC website.
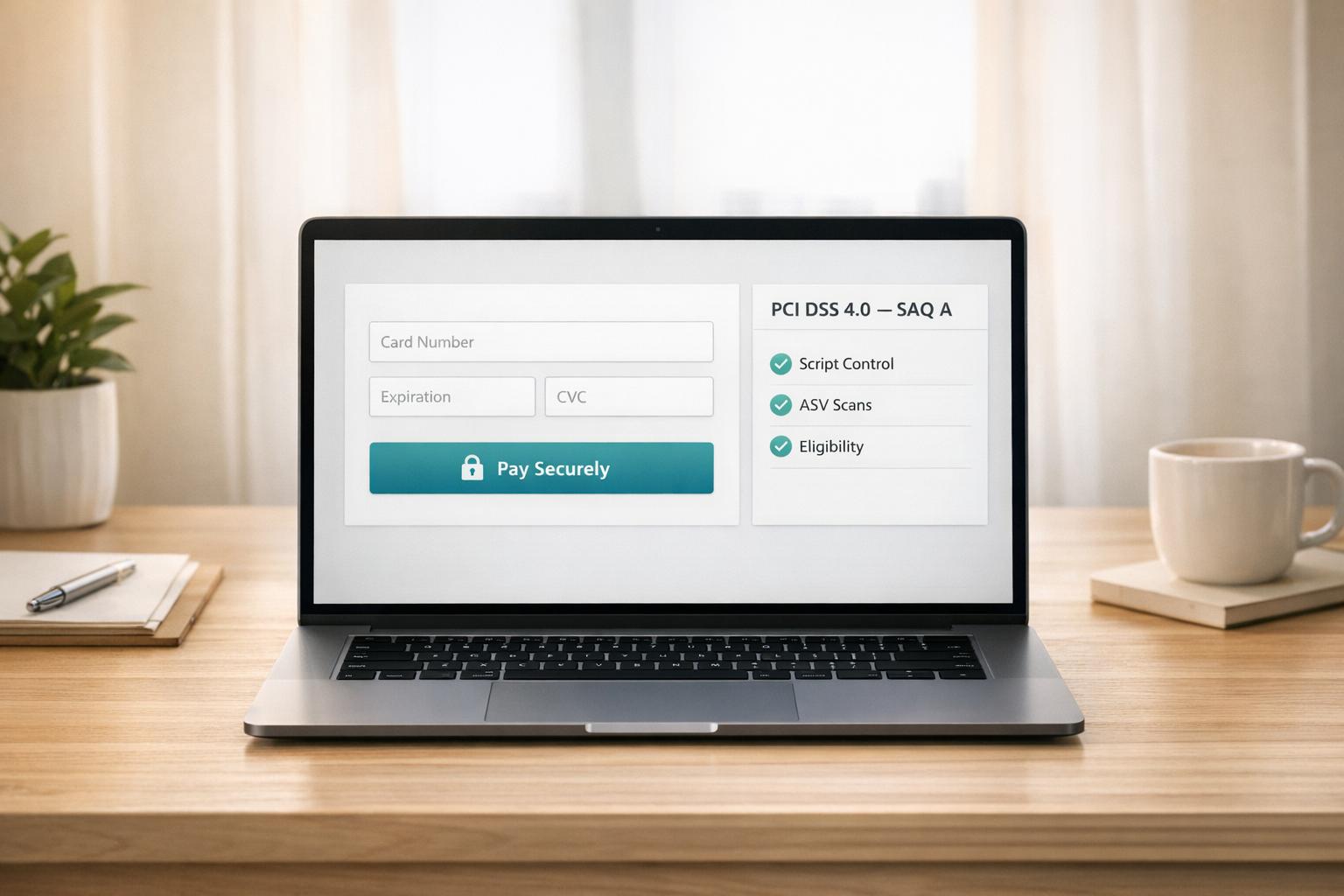
To avoid such pitfalls, prioritize tools designed with compliance in mind. Platforms like Reform, which offer features such as email validation, spam prevention, conditional routing, and real-time analytics, can help ensure that data remains within controlled environments. Reform’s lead enrichment capabilities, for example, enable businesses to collect necessary information without triggering unnecessary data transfers or exposing sensitive data.
When evaluating data collection tools, check for key elements like data storage practices, access controls, and built-in safeguards. Compliance doesn’t have to be overly complex - choosing platforms that integrate GDPR requirements from the start can significantly lighten the burden on your team.
Conclusion
Recent legal developments and compliance measures highlight the importance of proactive risk management in cross-border data transfers. EU court rulings now assign direct liability for such transfers, with potential penalties reaching up to 4% of global turnover, alongside individual awards and class actions. For example, the ILVA ruling in February 2025 clarified that GDPR fines must be calculated based on the worldwide revenue of an entire corporate group, not just the specific offending entity. Even minor breaches, as demonstrated in cases like Bindl v. European Commission, can lead to damages.
Adequacy decisions, such as the EU–US Data Privacy Framework, provide only temporary solutions. Although upheld by the General Court in September 2025, businesses should prepare fallback mechanisms like Standard Contractual Clauses to mitigate risks if the framework is invalidated in the future. This echoes the lessons learned from the abrupt collapse of the Privacy Shield in 2020, underscoring the need for adaptable compliance strategies.
Technical safeguards are just as critical as legal agreements. Tools and third-party integrations - such as analytics platforms, forms, or social login features - can inadvertently transfer data to non-EU servers, creating compliance risks. Opting for platforms designed with privacy in mind, such as Reform, which offers controlled data environments and features like email validation and spam prevention, can help reduce the likelihood of accidental violations while ensuring smooth operations.
The legal landscape has also shifted to make it easier for individuals to claim damages, even for minor breaches, as courts no longer require a minimum threshold for demonstrating harm. This change increases the stakes for businesses, making proactive compliance essential not just to avoid fines but also to maintain customer trust in an era of growing privacy litigation.
To stay resilient, organizations should focus on mapping data flows, auditing third-party tools, completing Transfer Impact Assessments (TIAs), and implementing strong technical safeguards. By integrating these steps with broader compliance efforts, businesses can better navigate the evolving regulatory environment. Treating data protection as a core operational priority - not just a legal formality - will position organizations to meet future challenges with confidence.
FAQs
When does remote access count as a GDPR “data transfer”?
Remote access is considered a GDPR "data transfer" when personal data can be accessed from outside the EU. This is particularly relevant if the data is shared or made accessible across borders without the necessary safeguards in place, as specified by the EDPB guidelines. To stay compliant, it's essential to grasp these regulations and establish proper protections for cross-border data access.
How do I know if encryption is enough to satisfy Schrems II safeguards?
Encryption plays a key role in securing personal data during transfer. However, relying on encryption alone isn't enough to meet the safeguards outlined in Schrems II. To fully comply, a transfer impact assessment is necessary. This assessment evaluates risks related to legal frameworks, government access, and technical vulnerabilities in the destination country.
Encryption should be combined with additional measures, such as contractual agreements and organizational controls, to create a comprehensive approach. These supplementary safeguards help ensure adherence to GDPR and Schrems II requirements, offering stronger protection for personal data.
What’s my backup plan if the EU–US Data Privacy Framework gets struck down?
If the EU–US Data Privacy Framework gets invalidated, businesses can turn to Standard Contractual Clauses (SCCs) as an alternative. While SCCs remain valid, they are under close examination, so it’s critical to ensure they meet EU standards. Additional measures, such as binding corporate rules or implementing data localization strategies, can help strengthen compliance. Keep an eye on evolving legal developments and work closely with privacy law experts to navigate potential restrictions and ensure your data transfers remain within legal boundaries.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)