Retail Payment Forms: PCI DSS Compliance Tips

Protecting customer payment data is non-negotiable. If you're handling card payments, compliance with PCI DSS (Payment Card Industry Data Security Standard) is not just a contractual obligation but also a critical safeguard against costly breaches and reputational harm. Here’s what you need to know:
- Why it matters: 66% of customers leave businesses after a data breach. The average cost of a breach for retailers? $4.45 million.
- What PCI DSS is: A set of 12 key requirements grouped into six goals, from encrypting data to limiting system access, aimed at keeping payment information secure.
- Core areas for compliance:
- Encrypt cardholder data and never store sensitive details like CVV or PINs after transactions.
- Secure your payment systems with firewalls, regular updates, and proper monitoring.
- Restrict access with multi-factor authentication and unique user IDs.
- Simplify compliance: Use third-party processors, hosted payment pages, or tokenization to reduce your compliance burden while improving security.
Bottom line: PCI DSS compliance isn’t just about avoiding penalties - it’s about protecting your business and your customers in an era where over 60% of consumer payments are made by card. Following these guidelines ensures your payment forms are secure, efficient, and trustworthy.

PCI DSS Compliance Statistics and Impact on Retail Businesses
PCI DSS Explained: What It Is, Who Needs It, and How to Comply | pTrackly

sbb-itb-5f36581
Core PCI DSS Requirements for Payment Forms
PCI DSS compliance for payment forms zeroes in on three key areas: encrypting cardholder data, securing the development environment, and restricting system access. These technical measures align with the broader PCI DSS goals to safeguard sensitive payment information. Let’s break down each core requirement for better integration into your payment forms.
Protecting Cardholder Data
Encryption is critical to keeping cardholder data secure and unreadable. Always use HTTPS on pages that handle payment data - this ensures information is encrypted as it moves between the customer’s browser and your server. Additionally, show only the last four digits of a card number and mask the CVV during entry. These steps help prevent "shoulder surfing" and reduce risks if someone gains unauthorized access to your systems.
"Encryption of cardholder data with strong cryptography is an acceptable method of rendering the data unreadable according to PCI DSS Requirement 3.5.1." – PCI Security Standards Council
Sensitive authentication data, such as full CVV codes, PINs, or magnetic stripe data, should never be stored after a transaction is completed. Many businesses adopt tokenization, which replaces card numbers with random tokens that are useless if stolen. This method can shrink your PCI scope by 80–90%. Considering that over 80% of data breaches involve weak or stolen passwords, encryption and tokenization are non-negotiable.
Building a Secure Development Environment
Your payment form’s infrastructure must be fortified against external threats. Start by configuring firewalls to isolate your cardholder data environment and deploying File Integrity Monitoring (FIM) to detect unauthorized changes.
Stay on top of security patches for POS systems, servers, and antivirus tools - apply them as soon as they’re available. Keep an updated inventory of all scripts running on your payment pages, and use Content Security Policy (CSP) headers to control which scripts are allowed to execute. This is especially important to guard against Magecart-style attacks, where hackers inject malicious code to steal card data during checkout. These precautions help reduce vulnerabilities in your payment forms.
Setting Up Access Controls
Beyond encryption and secure development, controlling access to your systems is equally critical. With 86% of data breaches driven by financial motives, limiting access to payment systems is a must. Only employees with a legitimate need should have access to cardholder data, and access should be strictly on a need-to-know basis. Assign unique user IDs to monitor activity and ensure accountability.
Replace all vendor-supplied default passwords immediately after installation, and enforce multi-factor authentication (MFA) for accessing the cardholder data environment. MFA is now required for all CDE access, not just remote connections, and passwords must meet a minimum length of 12 characters. These measures strengthen security and make it far more challenging for unauthorized users to infiltrate your systems.
How to Design PCI DSS-Compliant Payment Forms
Creating a PCI DSS-compliant payment form doesn’t mean sacrificing simplicity. The goal is to secure customer data while ensuring the checkout process remains quick and seamless. With e-commerce fraud expected to soar from $44.3 billion in 2024 to $107 billion by 2029, secure payment form design is more than a requirement - it’s a way to stay competitive.
Using Encryption and Secure Connections
Every payment page must run on HTTPS with TLS 1.2 or higher. SSL, being outdated, is no longer sufficient. This encryption ensures that data transmitted between the customer’s browser and your server is protected from interception.
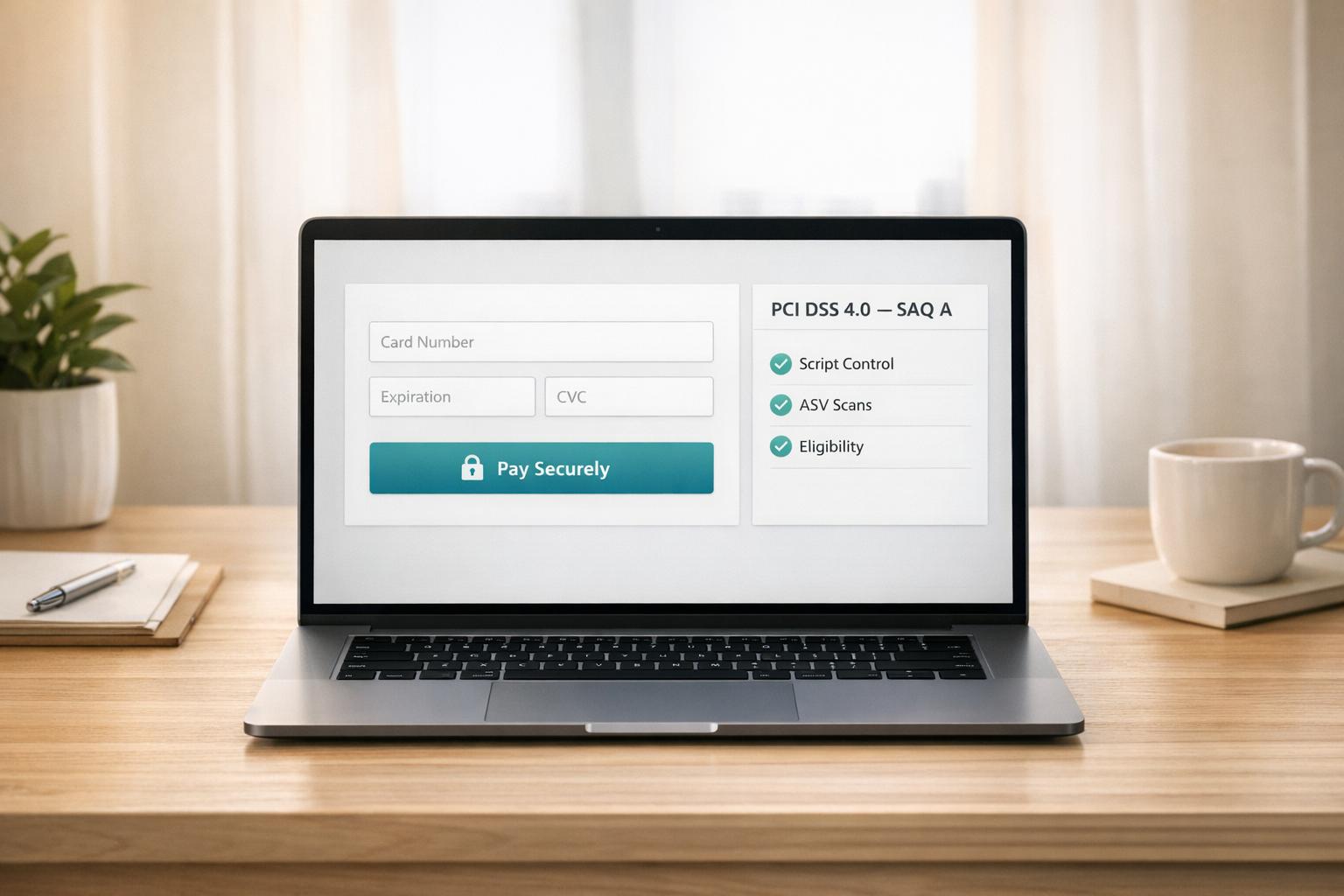
For added security, consider using hosted payment fields provided by services like Stripe or PayPal. These fields are embedded using iframes, meaning sensitive information - like card numbers - never touches your servers. This approach can significantly reduce your PCI DSS compliance requirements, shifting from the more complex SAQ D to the simpler SAQ A. If you’re building forms yourself, use secure APIs and integrate 3D Secure 2 for transaction validation.
"The tension between security and usability shows up most clearly at checkout. If you add too many security checks, customers might leave. If you strip too much away, you leave the door open for fraud." – Stripe
Once encryption is in place, the next step is designing a form that’s easy for customers to use.
Making Forms Easy to Use
Strong security is vital, but poor usability can drive customers away. With cart abandonment rates averaging 84.24%, every design detail counts. Your form must balance PCI DSS requirements with a smooth user experience.
Keep the form simple by asking only for essential information. For digital products, skip the shipping address entirely. For mobile users, optimize input fields - set card and CVV fields to "numeric" input mode to bring up numeric keypads. Enable autofill by using standard HTML autocomplete attributes like cc-number, cc-exp, and cc-csc to let browsers and password managers securely fill in details. Add real-time validation using the Luhn algorithm to catch card number errors and provide clear feedback for issues like expired dates or incorrect CVVs.
To build trust, display a "Secure checkout" label or a lock icon near the form. Allow customers to check out as guests, avoiding mandatory account creation, which often leads to frustration and abandonment.
Avoiding Common Compliance Mistakes
Even with secure design principles, some mistakes can derail compliance efforts. The most critical error is storing Sensitive Authentication Data (SAD) after authorization. This includes full CVV/CVC codes, PINs, and magnetic stripe data. Storing such data - even in encrypted form - violates PCI DSS rules. Use tokenization and masking to minimize PCI scope.
Another common issue is failing to protect against vulnerabilities like injection flaws. Payment forms must block SQL, LDAP, and command injection attacks to safeguard cardholder data. Automated security testing tools can help detect these vulnerabilities before deployment. Additionally, developers should undergo hands-on secure coding training annually, rather than relying on passive video courses.
Compliance isn’t a one-time effort - it requires ongoing vigilance. In 2018, nearly half (47.5%) of organizations failed interim PCI DSS assessments. To stay ahead, schedule quarterly vulnerability scans and annual penetration tests. Also, confirm that third-party payment processors or hosting providers you work with are PCI DSS compliant. Remember, the average cost of a data breach reached $4.88 million in 2024.
How to Reduce PCI DSS Compliance Scope
Managing PCI DSS compliance can feel overwhelming with all the controls and documentation involved. One effective way to lighten this load is by keeping cardholder data completely off your systems. By doing so, you not only simplify your compliance efforts but also enhance security.
"The single best security decision you can make is not to collect, transmit, or store cardholder data on your own infrastructure." – NOC
When payment data doesn't touch your servers, your compliance obligations shrink significantly. Instead, the responsibility shifts to specialized providers who are already PCI-certified.
Using Third-Party Payment Processors
One of the easiest ways to reduce your compliance scope is by using hosted payment pages. These pages redirect customers to platforms like Stripe or PayPal, where the entire transaction is processed on their PCI-certified servers. Since your system never interacts with the card data, you may qualify for SAQ A, the simplest self-assessment questionnaire.
If redirecting customers disrupts the checkout experience, hosted fields offer a seamless alternative. These secure iFrames allow customers to input payment details directly into the processor's system. The card data is transmitted securely, and your system only receives a token - completely removing sensitive data from your environment.
This approach also defends against web-skimming attacks (such as "Magecart"). Since 2005, over 10 billion consumer records have been compromised in more than 9,000 data breaches in the US. Hosted fields and external domains isolate payment data, making it inaccessible to malicious scripts on your site.
Another tool, tokenization, replaces card numbers with non-sensitive tokens. This allows for recurring payments without storing actual card data, further reducing your exposure.
For physical transactions, a different strategy is required.
Implementing Point-to-Point Encryption (P2PE)
In physical stores, Point-to-Point Encryption (P2PE) ensures card data is encrypted immediately at the terminal. The encrypted data remains secure until it reaches the processor's decryption environment, meaning it never exists in readable form on your systems.
Adopting a PCI-validated P2PE solution can drastically lower your compliance requirements. For example, under PCI DSS v4.0, switching from SAQ D to SAQ P2PE reduces the number of security controls you need to manage by almost 90%. Instead of answering 329 questions in SAQ D, merchants using P2PE only need to address 21 to 33 questions.
"Only Council-listed P2PE solutions are recognized as having met the rigorous controls defined in the PCI P2PE Standard for the protection of payment card data, as well as meeting the requirements necessary for merchants to reduce the scope of their cardholder data environment (CDE)." – PCI Security Standards Council
Before implementing P2PE, confirm that the solution is listed on the PCI Security Standards Council's website. Non-validated encryption solutions (often referred to as E2EE) don't provide the same automatic scope reduction. Additionally, you'll need to follow the P2PE manual precisely and conduct regular physical inspections of payment terminals to detect tampering.
With cyberattacks happening approximately every 39 seconds, P2PE offers a robust defense. By encrypting data immediately and keeping decryption keys out of the merchant's hands, intercepted data becomes useless - just meaningless characters. This makes P2PE a powerful tool for protecting sensitive payment information.
Validating and Maintaining Compliance
Achieving PCI DSS compliance is just the start. To maintain security, continuous validation through monitoring and regular assessments is a must.
Completing the Self-Assessment Questionnaire (SAQ)
The first step is selecting the correct SAQ version based on how you handle payments. For businesses that fully redirect customers to third-party processors like Stripe or PayPal, SAQ A (with 22 requirements) is appropriate. However, if you use JavaScript-based payment forms hosted on your website, you'll need SAQ A-EP, which includes 191 requirements.
"Choosing the wrong SAQ is one of the most common PCI DSS mistakes we see. Merchants regularly select a shorter questionnaire than their architecture requires, leaving them non-compliant without realizing it." – Lorikeet Security Team
Once you've determined the correct SAQ, ensure your system meets its eligibility criteria. Go through each requirement, marking them as "In place", "Not in place", or "N/A" after performing the necessary testing. For any unmet requirements, document a remediation plan. After completing the SAQ, submit it along with your Attestation of Compliance (AOC) and any required vulnerability scan reports to your payment processor. To stay on track, set a reminder 11 months after your last assessment to start the next cycle before your compliance expires.
Running Security Scans and Audits
To avoid falling out of compliance, conduct external ASV scans every 90 days. These scans must be carried out by a PCI SSC Approved Scanning Vendor (ASV) and typically cost between $100 and $500 per quarter.
Additionally, annual penetration testing is required to cover both internal and external systems. These tests generally range in cost from $2,000 to $15,000. If you make significant infrastructure changes, such as adding new systems or modifying firewalls, you'll need to repeat the tests.
Starting March 31, 2025, PCI DSS v4.0 will introduce new rules, including weekly automated checks for unauthorized changes to payment pages and bi-annual reviews of user access privileges. Service providers will also need to perform segmentation testing every six months instead of annually.
"PCI is VERY unforgiving if ASV scans do not occur within a 90-92 day cadence. Remedial or correction scans must be provided as soon as practicable to prove that the CDE was vulnerable for the shortest practical period." – Dick Hacking, Consultant, LevelBlue
These regular tests, combined with updated policies, help ensure your compliance remains intact.
Keeping Security Policies Current
Regular assessments and policy updates are essential to protect against new threats. For example, administrative passwords must now be at least 12 characters long, an increase from the previous 7-character minimum. Update your security awareness training annually, maintain an up-to-date software inventory, and ensure your incident response plans are ready.
Make sure to obtain current Attestations of Compliance (AOC) from your third-party payment processors to verify they meet PCI DSS standards for the services they provide. Remember, non-compliance can result in monthly fines ranging from $5,000 to $100,000, and a single security breach could cost a small business over $100,000 in liabilities.
Conclusion
Integrating PCI DSS best practices into your payment forms ensures both security and usability. Achieving PCI DSS compliance involves prioritizing data protection, secure systems, and controlled access. By combining strong security measures such as encryption, input masking, and mobile-friendly design, you can create a payment process that's both safe and user-friendly.
Using third-party processors and tokenization can simplify compliance significantly. For instance, merchants opting for fully hosted checkouts often qualify for SAQ A, which keeps sensitive data off their servers while still delivering a seamless, branded checkout experience.
"Meeting PCI requirements strengthens your overall security posture and helps build lasting customer relationships anchored with trust." – J.P. Morgan
With debit and credit cards making up over 60% of consumer payments, maintaining PCI DSS compliance is essential. It's not just about meeting standards - it’s about protecting your customers and reinforcing your business against evolving security threats.
FAQs
Which SAQ do I need for my payment form setup?
The type of SAQ (Self-Assessment Questionnaire) you need hinges on how your payment system is set up. For example, SAQ A is meant for merchants who fully outsource payment processing and handle only card-not-present transactions. On the other hand, SAQ D applies to businesses with more intricate payment environments. It's crucial to evaluate your system carefully to identify the right SAQ for maintaining PCI DSS compliance.
How can I keep card data off my servers to reduce PCI scope?
When it comes to reducing PCI scope, one of the best steps you can take is to avoid hosting payment forms on your own servers. Instead, consider these alternatives:
- Hosted payment fields or tokenized iFrames: These allow customers to enter their card information directly into your payment service provider's (PSP) secure environment, keeping sensitive data off your systems.
- Hosted payment pages or redirects: This method redirects users to your PSP’s domain to complete the transaction, ensuring that payment data never touches your infrastructure.
For an even more streamlined approach, you can outsource the entire payment processing operation to a PCI-certified provider. This significantly reduces your compliance responsibilities and keeps your PCI scope as minimal as possible.
What changes does PCI DSS v4.0 require by March 31, 2025?
By March 31, 2025, PCI DSS v4.0 introduces several new security requirements. These include adopting proper DMARC protocols to bolster email security, deploying web application firewalls for internet-facing applications, and enforcing tighter access controls to safeguard cardholder data. Additionally, organizations are required to implement more robust password policies and use multi-factor authentication where necessary to strengthen overall security measures.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)