How Tokenization Simplifies PCI DSS Compliance

Tokenization makes PCI DSS compliance easier by replacing sensitive credit card data with random tokens that hold no value to hackers. This reduces the systems and processes that need to meet PCI requirements, cutting compliance efforts by up to 90%. Sensitive card info is stored securely by a certified provider, leaving businesses to focus on protecting only token-handling systems. Key benefits include:
- Reduced PCI scope: Fewer systems to secure and audit.
- Lower costs: Simplified audits and fewer compliance tasks.
- Improved security: Tokens are useless if stolen.
- Adaptation to PCI DSS 4.0: Meets stricter, continuous validation rules.
PCI DSS Compliance Challenges

Common PCI DSS Compliance Problems
Meeting PCI DSS requirements goes far beyond simply passing an annual audit. Businesses must manage a wide range of security controls across networks, databases, applications, and personnel. Without a dedicated compliance team, this can feel like an impossible task.
One major hurdle is data sprawl. Primary Account Numbers (PANs) often show up in unexpected places - like server logs, analytics tools, error trackers, or data lakes. Every time a PAN interacts with a new system, that system becomes part of your Cardholder Data Environment (CDE). This means more controls to implement and document, making compliance even more complex.
The introduction of PCI DSS 4.0, mandatory as of March 2025, brought a major shift. Instead of focusing on "point-in-time" audits, the new standard requires continuous validation. Businesses now need to prove their controls work every day, not just during an audit window. However, as of early 2025, only 32% of organizations felt fully prepared for these requirements, and 72% hadn't yet figured out the necessary investments in people, processes, and technology to meet the new expectations.
The financial risks of non-compliance are steep. Fines can range from $5,000 to $100,000 per month, and the average cost of a payment card data breach exceeds $4 million. Beyond fines, businesses could lose their ability to process card payments entirely - a devastating outcome for companies reliant on credit and debit transactions.
These challenges become even more daunting when addressing the specific security needs of payment forms.
PCI DSS Requirements for Payment Forms
Payment forms are under stricter scrutiny than ever under PCI DSS 4.0. The updated standard requires businesses to address client-side vulnerabilities - threats that occur in the customer’s browser rather than on the server. Traditional server-side security measures often miss these issues, such as formjacking attacks where malicious code silently captures card data.
Requirements 6.4.3 and 11.6.1 specifically focus on third-party scripts used on payment pages. Modern interactive checkout forms often depend on 50 to 100 scripts for functions like analytics, chatbots, A/B testing, and tag management. Under PCI DSS 4.0, businesses are now responsible for ensuring the integrity and authorization of every single script that interacts with payment fields. This is especially urgent given the nearly 300% rise in e-commerce domains with payment page skimmers in 2024.
The risks are real. In 2018, British Airways suffered a breach when malicious JavaScript injected via a third-party script compromised around 380,000 card transactions, including CVV codes. Despite having PCI certification, the company was fined £20 million under GDPR due to these client-side vulnerabilities. Similarly, Ticketmaster saw over 40,000 customer records stolen when a third-party chatbot script was compromised, leading to lawsuits.
Tracking scripts manually is both time-consuming and expensive, costing about $35,000 annually and requiring 160–200 hours per year. On top of that, PCI DSS 4.0 mandates several other measures, including Multi-Factor Authentication (MFA) for all CDE access, 12-character minimum passwords, and DMARC implementation to prevent phishing attacks via email.
"PCI DSS 4.0 is the most significant update to the standard in over a decade. For merchants, it means higher expectations and more ongoing scrutiny." - Payrails
The updated standard also adds to the documentation burden. Under PCI DSS 4.0, if a security process isn’t documented, auditors may treat it as if it doesn’t exist. This means businesses must maintain detailed, audit-ready records for everything - access logs, change approvals, vulnerability fixes, and script authorizations - on an ongoing basis.
Tokenization offers a way to reduce these challenges by limiting data exposure and easing compliance efforts.
sbb-itb-5f36581
Data-Centric Security as a Business Enabler: Turning PCI DSS v4.0 Compliance into Success
What Is Tokenization and How It Works
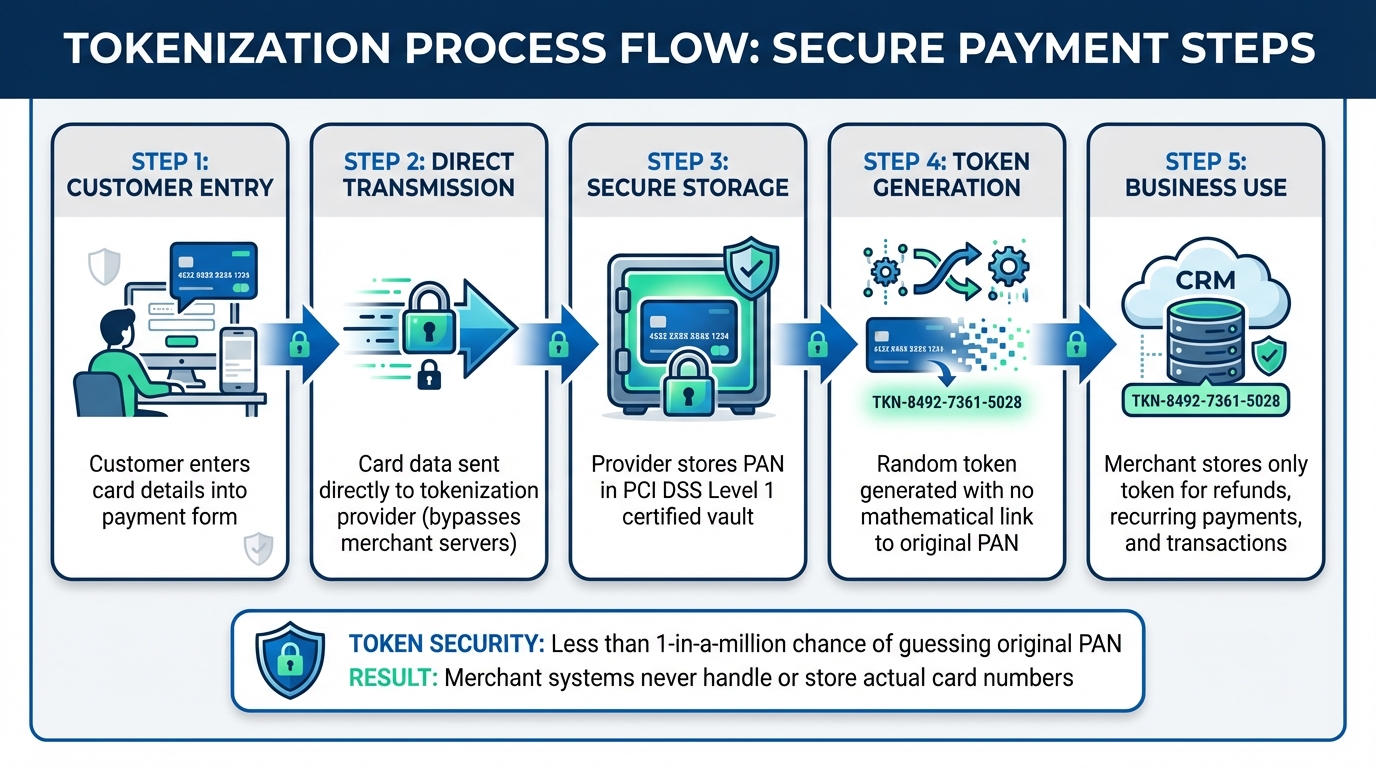
How Tokenization Works: 5-Step Process for Secure Payment Processing
Tokenization Defined
Tokenization is a process that replaces sensitive cardholder data - such as the Primary Account Number (PAN) - with a unique, randomly generated identifier called a token. This token acts as a stand-in for your credit card number, but it holds no exploitable value on its own.
Unlike encryption, which scrambles data using reversible algorithms, tokenization creates tokens that have no mathematical link to the original card data. This means if someone intercepts a token, they can't reverse-engineer it to uncover the actual PAN. The real card information is securely stored in a centralized token vault, typically managed by a service provider certified at PCI DSS Level 1.
Here’s how it works in practice: when a customer enters their card details into a payment form, the data goes directly to the tokenization provider. The provider securely stores the PAN in its vault and sends a token back to your business. From there, you store only the token in your systems - like your CRM or database - for future use, such as processing refunds or repeat transactions. This way, your environment never handles or stores the actual card number.
A robust tokenization system ensures there’s less than a one-in-a-million chance of guessing the original PAN. Many systems also use format-preserving tokens, which keep the 16-digit structure of a credit card number. This compatibility helps avoid disruptions to current business processes and validation systems. Beyond just protecting sensitive data, tokenization also reduces the complexity of compliance.
Tokenization and PCI DSS Scope
By ensuring that sensitive card data never enters your systems, tokenization significantly reduces the scope of PCI DSS compliance. Instead of completing the extensive SAQ-D form, businesses can often shift to the simpler SAQ-A. With automation and tokenization, merchants can cut up to 90% of the time and effort required for PCI compliance.
However, tokenization doesn’t entirely remove compliance responsibilities. The PCI Security Standards Council states, "Tokenization solutions do not eliminate the need to maintain and validate PCI DSS compliance, but they may simplify a merchant's validation efforts by reducing the number of system components for which PCI DSS requirements apply". Businesses still need to secure the systems that capture cardholder data and ensure their tokenization provider adheres to compliance standards.
Choosing the right tokenization partner is crucial. Look for a provider with PCI DSS Level 1 Service Provider certification and an annual Attestation of Compliance (AOC). This ensures the provider is responsible for securing the token vault and raw cardholder data, leaving you to focus on safeguarding the entry points where customers input their information. Next, we’ll discuss the key factors to consider when selecting a reliable tokenization provider.
How Tokenization Simplifies PCI DSS Compliance
Reducing PCI DSS Scope
Tokenization helps streamline PCI DSS compliance by significantly shrinking your Cardholder Data Environment (CDE). When sensitive card data is sent straight to a secure, third-party vault using tools like iFrames or hosted payment fields, your servers and systems never directly process or store raw card data. This means your infrastructure is effectively removed from PCI DSS scope.
As Jonathan Paolozzi explains, "if the card data is sent directly to the tokenization service without passing through the merchant's infrastructure, the CDE is limited to only the initial point of entry and the tokenization system".
By outsourcing the handling of raw card data to a third-party provider, you can bypass about 95% of PCI DSS requirements. Instead of managing over 300 security controls across your entire system, your focus narrows to securing the entry points where customer data is entered. Since tokens replace sensitive card data in your CRM, analytics tools, and customer databases, any potential breach would yield useless information for attackers.
On top of that, completing SAQ-A (Self-Assessment Questionnaire A) becomes much faster - taking just a few days compared to the weeks required for SAQ-D. This time-saving aspect ties directly into another key benefit: outsourcing compliance responsibilities.
Outsourcing Compliance Responsibilities
Tokenization not only simplifies your compliance efforts but also transfers a portion of the responsibility to your provider. When you work with a PCI DSS Level 1 Service Provider, they take charge of securing the token vault, managing data during transmission, and maintaining the systems that store actual card numbers.
This arrangement means you no longer need to worry about managing cryptographic keys or ensuring the security of the vault. Your provider handles these complex tasks, allowing you to focus on your core business operations while maintaining peace of mind about data security.
Benefits of Tokenization for Payment Forms
Tokenization does more than just shrink your PCI scope - it bolsters security, trims costs, and aligns with evolving compliance standards.
Improved Security
Tokenization swaps out your customers' Primary Account Numbers (PANs) with random strings that bear no mathematical connection to the original data. Unlike encryption, which can be decrypted with the right key, tokens are impossible to reverse-engineer into the original cardholder information. This makes stolen tokens practically useless outside of your specific processing environment. Mike Riesen from SecurityMetrics explains:
"The best part of a correctly implemented tokenization system is that merchants never see customer credit card information. They only see tokens, which are essentially useless strings of information".
Given the financial impact of data breaches, this added layer of security is critical for protecting your business.
Lower Costs and Better Efficiency
Tokenization slashes compliance costs by significantly reducing the systems that fall under PCI DSS audit scope. Instead of auditing your entire infrastructure, your efforts (and expenses) focus only on the entry points where customer data is collected. This means cheaper audits and less paperwork.
Beyond compliance, tokenization simplifies operations. For recurring payments or subscriptions, network tokenization automatically updates expired or replaced card details, reducing transaction declines and customer churn. This leads to higher payment success rates and less operational hassle. The cost? Typically $0.02–$0.10 per transaction - a fraction of the potential non-compliance fines, which range from $5,000 to $100,000 per month.
Adapting to PCI DSS Changes
PCI DSS 4.0 introduces a shift from periodic audits to continuous security validation. Tokenization helps you stay ahead by offering clean, centralized logs for monitoring data access. While only 32% of organizations feel fully ready for the PCI DSS 4.0 transition as of early 2025, a strong 74% already rely on tokenization as their primary compliance strategy. This combination of security and efficiency makes tokenization an essential tool for modernizing your payment forms.
Implementing Tokenization for Secure Payment Forms
Step-by-Step Tokenization Process
To harness the security advantages of tokenization, you need a clear, structured approach to implementing it within your payment forms.
Start by mapping every system that interacts with payment data. Create a detailed card flow diagram to pinpoint exactly where cardholder data is stored, transmitted, or processed - whether it’s through billing systems, support platforms, or analytics tools. This step is essential for ensuring effective protection.
Next, choose a PCI DSS Level 1 provider. Look for one that undergoes regular audits and provides an Attestation of Compliance (AOC). By partnering with such a provider, you can offload much of the security responsibility to experts in safeguarding payment data. Then, integrate tokenization at the point of data capture. This can be done using hosted payment pages, iFrames, or client-side SDKs, ensuring card numbers are tokenized before they ever reach your servers.
Your provider will store the sensitive card data in a secure vault and return a token for your use. During this process, safely migrate any existing card numbers to the tokenized system and delete the raw data from your environment. Update your internal systems - like billing, refunds, and recurring payments - to use tokens instead of raw card details. Be sure to rigorously test all payment scenarios to confirm everything works smoothly. This approach not only enhances security but also reduces your PCI compliance scope.
Once these steps are complete, you can further strengthen your payment forms by following key best practices.
Tokenization Best Practices
To fully leverage the benefits of tokenization, keep these best practices in mind.
Start tokenizing as early as possible in the payment process. Using hosted fields ensures that sensitive data never enters your environment. If your legacy systems require 16-digit values for routing or analytics, choose a provider that offers format-preserving tokens. This way, you can maintain compatibility with existing database structures and validation rules.
Never store tokens and raw card data together in the same database. Doing so makes it almost impossible to prove to auditors that the sensitive information has been fully removed. Enforce strict access controls for detokenization processes and maintain detailed audit logs. While tokenization protects data at rest, ensure all data in transit is encrypted using TLS when communicating with your tokenization provider. As Mike Riesen from SecurityMetrics explains:
"Tokenization is more about implementation than the actual technology".
Finally, conduct regular compliance checks to ensure your tokenization setup aligns with evolving PCI DSS standards. By combining tokenization with automation, you can reduce up to 90% of the time and effort typically required for maintaining compliance.
Conclusion
Tokenization fundamentally changes how businesses manage sensitive card data, streamlining PCI DSS compliance. Instead of juggling complex security measures across numerous systems, this method shifts the responsibility to a certified tokenization provider. Your internal systems only handle non-sensitive tokens, making audits simpler, reducing costs, and lowering risks.
The financial stakes are high. Data breaches involving payment cards average over $4 million in losses, while non-compliance fines can range from $5,000 to $100,000 per month. Tokenization provides a clear solution to these challenges. When paired with automation, it can cut 90% of the time and effort typically required for PCI compliance. For example, businesses can transition from lengthy SAQ-D assessments to the much simpler SAQ-A questionnaires.
Tokenization also unlocks opportunities for modern payment solutions. It supports features like recurring billing, one-click checkouts, and seamless omnichannel transactions - all without increasing your security burden. As Jonathan Paolozzi, Head of Cybersecurity at Curbstone, puts it:
"The merchant is responsible for securing their components, but the tokenization provider is responsible for the data while in transit and while in their vault – eliminating most, if not all, of the security and compliance burden for the merchant".
FAQs
Does tokenization eliminate PCI DSS compliance?
Tokenization doesn’t remove the need for PCI DSS compliance, but it makes the process much simpler. By swapping out sensitive payment data with non-sensitive tokens, it reduces the areas that need to meet compliance standards. This approach helps cut down security risks and eases the overall workload tied to compliance.
What remains in PCI scope after tokenization?
Tokenization helps reduce the exposure of sensitive payment data, such as the primary account number (PAN), but it doesn't completely remove it from PCI scope. This is because the original data is still securely stored in vaults, meaning it hasn't been eliminated or replaced. While tokenization minimizes risk, compliance still demands that sensitive data be managed carefully within secure environments.
How do I choose a PCI Level 1 tokenization provider?
When selecting a PCI Level 1 tokenization provider, focus on their ability to securely substitute sensitive card data with non-sensitive tokens. Verify that they meet PCI DSS compliance standards and can handle your specific transaction channels and volume requirements. Additionally, assess their track record and experience in providing dependable and compliant tokenization services.
Related Blog Posts
Get new content delivered straight to your inbox

The Response
Updates on the Reform platform, insights on optimizing conversion rates, and tips to craft forms that convert.
Drive real results with form optimizations
Tested across hundreds of experiments, our strategies deliver a 215% lift in qualified leads for B2B and SaaS companies.


.webp)








